Use it to link your GitHub account, Twitter, Bitcoin address, and Facebook. This .onion link makes it impossible for hackers to impersonate your profile. Also, you can set a strong password to protect your message and choose how long it will take to expire. The good news is that the platform will not see what you copy/paste.
Stolen Data And Identity Theft

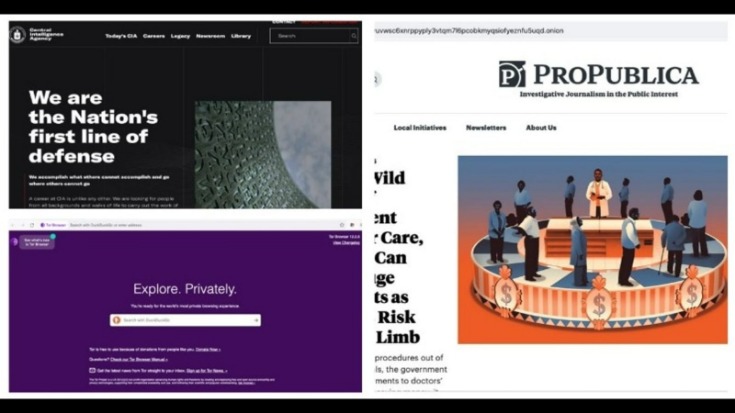
One of the challenges of exploring the dark web is that you can’t just use a search engine and type in what you’re after like you would on the surface web. Instead, you often have to consult directories to find lists of legitimate sites and visit and access them that way or use special dark web-friendly search engines. The victim types in their information, thinking they’re accessing a site that they know and trust, but they’re actually giving away their data. There are a lot of these sites across the dark web, which is why you have to be extra careful.
Download And Connect A VPN
Once the installation process is complete, you’re ready to start setting up your overlay network. All you need to do is download and install the app from the website – torproject.org. All jokes aside, you can see pretty much the same stuff as on the surface web, with a few spicy additions that you can’t find otherwise.
- Tor anonymity comes with a cost since malicious hackers and criminals like to operate in the shadows.
- Journalists, activists, and individuals concerned about privacy and censorship often use the dark web to communicate securely and anonymously.
- With this setup, your ISP sees Tor usage, and your VPN provider sees the final traffic after it leaves Tor.
- We already went through VPNs, anonymizing web browsers, and disposable operating systems, so I won’t bother reminding you about those.
- It is a component of Whonix, an operating system that functions as a whole inside a virtual computer.
- Just turn on your VPN, wait for the connection to stabilize, and launch Tor.
Is Using The Tor Network Illegal?
Well, now it’s time to fire up Tails and do a little bit of tinkering. Note that the process can take anywhere from 5 to 30 minutes depending on your machine. Choosing Tor over standard browsers is crucial for dark web navigation due to its unique privacy features.
Plan Ahead Before Connecting
To access the Dark Web, you cannot simply type a URL into a standard browser. Instead, users must use specialized browsers designed to provide a high level of anonymity. By following these steps, you are on your way to exploring the hidden depths of the internet and enjoying a heightened level of online privacy and anonymity. If you need a way to organize as an activist or you want to discuss censored topics with others, my first suggestion is to stick to offline meetups. The second, less secure option is to use encrypted messaging apps with ties to specific non-profit or activist organizations. For example, Briar is an extremely private chat app designed to help journalists communicate anonymously with sources.

Why Are The Old onion Links No Longer Working?
Even if you’re only attempting to visit legitimate sites, one wrong click could expose you to content you would rather not see. To minimize the risk, research and verify sites before visiting them. Given the prevalence of malware across the dark web, it’s vital to have antivirus software installed and active on your device when accessing it. However, note that a VPN is not a definitive or comprehensive form of protection. It won’t guard you against all of the many threats that exist on the dark web, from phishing scams to malware and malicious sites.
Yes, Tor is available for free on iPhone through the Onion Browser (recommended by the Tor Project). This Dark Web browser allows you to connect to the Tor network on iOS devices, providing Tor’s privacy features without any cost. You can easily set up Tor on your iPhone, but you do need to use Orbot for it to work. Similarly, the Onion Browser also has 3 security levels — Gold, Silver, and Bronze.
Can I Get In Trouble For Accessing The Dark Web?
This means you can’t simply replace .com with .onion and expect it to work. The Onion Browser is far from ideal, but that’s entirely thanks to Apple’s policy of policing what iOS users can and cannot do on their own devices. However, unfortunately, it’s the only option for iPhone and iPad users. It’s crucial to download the Onion Browser on your iOS device by going through the website. For this reason, iPhone and iPad users can’t use the real Tor Browser app. And, in any case, I find Tor to be the best overlay network – and the easiest to use.
Keep your personal details secure by using aliases and anonymous email accounts when creating dark web accounts. Using secure, anonymous tools helps protect your identity from potential threats on the dark web. You can conduct discussions about current events anonymously on Intel Exchange. There are several whistleblower sites, including a dark web version of Wikileaks.
While this is not much compared to standard email services, it is enough for PGP-encrypted messages. The social media giant is also aware of the many attempts by repressive regimes to restrict its access. After all, it enables users to connect and communicate with each other from around the world. Since Hidden Wiki maintains all kinds of websites, ensure you don’t open something you don’t want to see. For that, vpnAlert provides you with objective VPN reviews, as well as comprehensive guides and tutorials.
Avast BreachGuard scans the dark web and will alert you immediately if and when it detects your personal data. BreachGuard will guide you through the process of recovering your accounts, helping you lock them down before a hacker can use your leaked credentials. Some hackers offer ransomware as a service (RaaS), where cybercriminals can “rent” a strain of ransomware from its creator in exchange for a fee or a percentage of their ransom payments. Others sell software exploits that other cybercriminals can use to infect victims with malware and steal personal data.
- Although the underground internet world is rife with everything bad, it also hosts positive elements.
- Avast BreachGuard scans the dark web and will alert you immediately if and when it detects your personal data.
- Unlike traditional browsers, this will route your internet traffic through an anonymising network and mask your IP address.
- Crimes range from data theft and selling illegal goods for cryptocurrencies to human trafficking and more severe offenses.
- Tor Browser is pre-configured with privacy settings optimized for secure browsing, so you can enjoy a higher level of anonymity right from the start.
These malware are more common on the dark web, as they would be blocked by Internet providers. Depending on the dark websites you visit, there can be hundreds of different malware strains you can run into. For example, there’s a malware called “CoinMiner” that can infiltrate your computer hardware to utilize your CPU or RAM for mining cryptocurrency. There are also remote access trojans, such as “Agent Tesla,” that can be launched to steal passwords.
Ways Small To Midsize Businesses Can Stay Safe In The Cloud
You can access the dark web on mobile with a dedicated dark web browser app. Install a mobile dark web browsing app — like Tor browser for Android or the Onion browser for iPhone — and enter an onion URL to start browsing. Researchers from Recorded Future estimated that while there are more than 55,000 existing onion domains, only 8,400 (or roughly 15%) of these sites were active.