
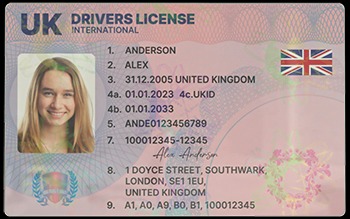
A fake ID might be ordered online in California, produced in a basement in New York, shipped through Texas, and ultimately used in Florida—creating significant challenges for law enforcement. Our customization process ensures your ID doesn’t just look real—it fits your story. With us, you get an ID that’s tailored to you, down to the smallest detail. We also include raised text, microprinting, and tamper-proof holograms that mimic state-issued cards down to the smallest detail. These features ensure that our IDs not only look the part but also perform seamlessly in real-world scenarios.
Are AI-generated Fraud Tools A Key Risk
Platforms like ProKYC provide full-service options for creating fake IDs, complete with images, videos, and the ability to bypass verification systems that use phone cameras or webcams. For less than $700 a year, cybercriminals can access these services, enabling them to generate fraudulent passports and even selfie videos for identity verification processes. These services have opened up a new avenue for ID fraud, making it more accessible than ever before.
Auto-Phishing: AI-Driven Social Engineering
Synthetic ID fraud creates fabricated identities using names, addresses, birthdates, and Social Security Numbers (SSNs) from different people. Once assembled, the fabricated ID can be used to apply for bank accounts, credit, loans, and government benefits. As organizations expand into new markets, understanding local fraud risks and delivering consistent, accurate verification processes becomes increasingly complex. Veriff’s IDV solution offers the perfect balance of robust fraud prevention and an optimized user journey.
Data Breaches And Identity Theft

In one notable case, cybercriminals used a deepfake video impersonating the CFO of a multinational corporation to successfully authorize the fraudulent transfer of $3.5 million to offshore accounts. The targeted company’s employees, thoroughly convinced by the authenticity of the AI-generated video conference, processed the payment without suspicion. The fraud was only discovered days later, long after the attackers had laundered the funds.
We caught 84% of the AI-generated fake IDs with image and symbology analysis alone. When combined with third-party database checks, we were able to catch 99.6% of the fraudulent IDs. We purchased 200 AI-generated fake ID images and ran them through our digital ID verification software.
- Additionally, increased enforcement measures necessitate higher governmental expenditures funded through public resources, placing an economic burden on taxpayers.
- Because of this, some people use it to get around government restrictions, while others use it for illegal activities like smuggling drugs and weapons.
- In interviews conducted at five major universities, approximately 30% of undergraduates admitted to having possessed or used a fake ID at some point.
- Amir, from a suburb near Mumbai, demonstrated how he verified a fake ID using a blockchain wallet.
- It’s known for its accessible pricing and a streamlined ordering process.
Top 7 Dark Web Marketplaces
As counterfeiting techniques become more advanced, the importance of integrating dynamic verification technologies—such as biometric authentication, blockchain verification, and AI-driven fraud detection—cannot be overstated. Enhanced cooperation between federal, state, and local law enforcement, combined with robust private sector partnerships, will be essential in closing the loopholes exploited by counterfeiters. The investigation combined traditional techniques like confidential informants with advanced digital forensics, tracing cryptocurrency transactions and deploying undercover agents in online forums. Prosecutors ultimately secured convictions against seven individuals on charges including document fraud, money laundering, and conspiracy. Launched in 2023, STYX focuses on financial crime, providing stolen credit card data, hacked bank accounts and access to various cryptocurrency laundering tools.
The Business Risk: What Fake ID Users Mean For Your Bottom Line

All dark web data and prices were pulled from SafetyDetectives’s dark web research team. If you want to increase the level of security across your desktop and mobile devices, read through some of our top antivirus, anti-spyware, and password manager reviews, including Norton, Dashlane, Bitdefender, and Malwarebytes. As you become increasingly connected to the digital world, it’s important to stay vigilant and aware of all the invisible dangers hiding on the web. Among the education documents that can be purchased via the dark web are high school diplomas, bachelor’s degrees, and master’s degrees.
Cost Vs Consequences
The VPN will protect your traffic when you connect with military-grade AES 256-bit encryption. This is high-level protection; no one can intercept your data or activities. It has a proprietary onion site in the Tor network to give you safe access even if your country restricts VPN usage.

Meanwhile, in Phoenix, Arizona, authorities traced a series of identity theft cases to a single source of fake IDs. The documents, which featured accurately reproduced holograms and microprinting, were linked to over $2.1 million in fraudulent credit card applications and retail purchases before the producers were apprehended. However, businesses must remain vigilant, as fraudsters are constantly refining their techniques to bypass current detection methods.
What A Real ID Is And What It’s Not

These are private and secure payment options to avoid exposing financial information. In certain orders, we will add cheap but heavy objects to the shipping container. This method of disguise is done to add to the illusion that a different product is inside. Then, we add documentation on the outside of each package, so it doesn’t have to be opened. Your fake ID will be shipped to you quickly and discreetly so that you can spend more time partying and less time waiting.
Some platforms rely less on full image generation and more on intelligent templating. Users upload a photo, select a document type from a list of supported countries, and the system assembles a realistic ID using predesigned layouts. These tools often simulate features such as holograms or plastic reflections so the ID appears as if it were photographed on a real surface. OnlyFake, discussed earlier, is an example of a platform offering streamlined document creation with country-specific customization. For individuals and organizations trying to protect themselves, relying solely on conventional KYC protocols may no longer be enough.
These tools can analyze data patterns, flag inconsistencies invisible to the human eye, and adapt as fraud techniques evolve. Fake ID users aren’t just a nuisance; they pose a serious threat to your business’s financial health and reputation. The risks go far beyond minor inconveniences, digging straight into your revenue, compliance responsibilities, and customer relationships. Fake IDs range from $100 to $300, with premium options mimicking real IDs through features like scannable barcodes and holograms, as noted by the Northwestern Business Review. While these prices may seem affordable to buyers, the risks to businesses are severe. One oversight can lead to fines, license suspensions, or even closures – not to mention lasting reputational damage.
OnionName lets you generate an .onion domain name that starts with a specific keyword — like onionamev33r7w4zckyttobq3vrt725iuyr6xessihxifhxrhupixqad.onion/, which is OnionName’s dark web link. The keyword in that example is “onioname,” which is right at the start of the .onion link. With a readable site name like that, people will know what to expect when they click on the link.


