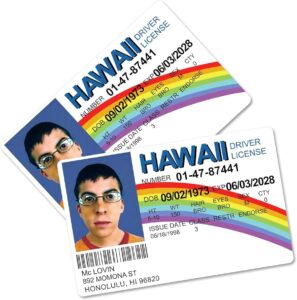
Across our study, we found 24.2% of AI-IDs showed evidence of photo tampering. While not always obvious to the human eye, verification systems identified the smallest discrepancies in document tampering. While a positive for businesses that have implemented a document tampering solution, it’s evidence that barcode and OCR validation alone may not be enough to identify evidence of tampering.

What Is The Dark Web Forum? Why Do These Exist?

Journalists in overly restrictive countries also appreciate the anonymity of the dark web. The majority of the web is called the “deep web” (often referred to as the “invisible” or “hidden” web). The deep web is basically all the content that you can’t find using Google or Yahoo search. So, sites that contain a domain extension like .com, .org, .net, .biz, .info, etc. can be found on the surface web.

Facebook — Dark Web Version Of Popular Social Media Site
- The last thing you need to do is to start researching vendors and determine what marketplace is a possible vendor to buy the products from.
- To protect oneself from identity theft, it is recommended to use the best VPNs to encrypt communications, practice safe ATM habits, maintain account and password hygiene, and avoid public or unsecured Wi-Fi.
- With appropriate ethical safeguards, our team also monitored online forums where fake IDs are advertised and reviewed, documenting the sophisticated marketing techniques employed by vendors.
- Our IDs feature tamper-proof overlays, weather-resistant finishes, and a smooth, polished look that mirrors the exact feel of genuine identification cards.
- ProPublica is a popular online publication that won five Pulitzers in 2016.
In the European Union, fraud rates are more evenly spread—passports and driving licenses both have a fraud rate of 0.82%, while ID cards show slightly higher risks. These patterns highlight the need for region-specific identity verification strategies to effectively combat document fraud. Fake IDs are commonly used across the US to purchase alcohol or access age-restricted services, creating challenges for businesses and law enforcement. This underground marketplace thrives on anonymity and cryptocurrency transactions, making it particularly attractive for those seeking to conceal their identities or bypass legal restrictions. Despite their allure, these fraudulent documents come with substantial risks, both legally and personally.
Types Of Stolen Cards
The goal of an anonymous and privacy network, Tor, is not to engage in the extensive collection of data. However, data is required for understanding, monitoring, and improving the network. Furthermore, data will help to detect attacks against the network and possible censorship events.
See Our Age Verification Process In Action!
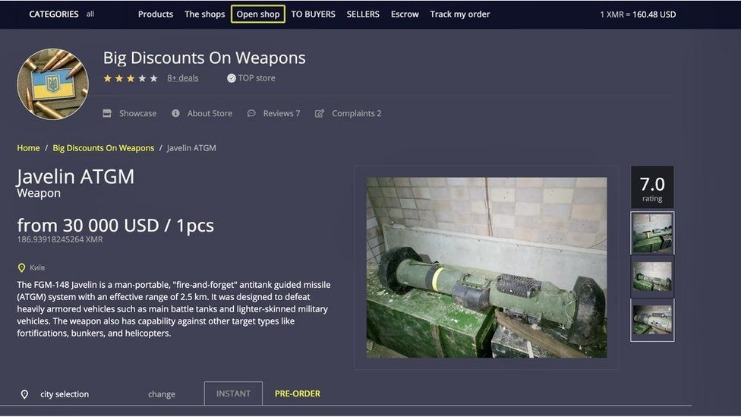
Despite growing crackdowns from law enforcement agencies, the dark web remains a hotbed of criminal activity, offering everything from drugs to stolen data. IDScan.net offers the leading AI-powered identity verification platform focusing on age validation and fraud reduction for compliance in both digital and physical environments. The quality of fraudulent IDs has always varied – from obvious fakes, easily caught by the naked eye, to high-quality fake IDs, only detectable with specialized authentication hardware and software. Authentic state-issued and government identification cards are in fact very high-quality documents that are constructed in layers to enable a wide variety of security features to be imbedded into them. The materials are costly and the process intricate and time consuming.
Understanding how fake documents originate, why they are popular, and the severe consequences of their use is essential to navigating and safeguarding oneself in today’s digital landscape. The dark web, a notorious portion of the deep web, is infamous for its ties to criminal activities and illegal products and services. It is no surprise that high-quality fake IDs can be found lurking within the dark corners of this hidden realm. However, acquiring counterfeit documents from the dark web carries risks, such as committing a criminal offense, receiving subpar documents, and increased potential for identity theft and financial fraud. The sooner you become aware of compromised information, such as stolen credit card numbers on dark web, the faster you can take steps to mitigate damage.
Implementing a robust ID verification solution into your screening process is crucial, as it allows property managers to quickly and accurately verify the authenticity of an applicant’s identification documents. In that case, it opens up a whole new set of problems for property managers, as they may be housing individuals with criminal records or outstanding warrants. In some cases, these individuals may even use these properties as a base for conducting illegal activities.
August’s Top VPN Discounts
In this instance, too, it is important to use a logless VPN and pay with Bitcoin if you can to stay anonymous. The VPN over Tor technique is also susceptible to an end-to-end timing attack, though it’s highly unlikely. Another vital precaution is to ensure that your .onion URLs are correct. Onion URLs generally contain a string of seemingly random letters and numbers. Once you are certain that you have the correct URL, save it in an encrypted note—the Tor browser will not cache it for later.
Stay Safe On Dark Web Websites
Purchasing and using fake IDs or fraudulent documents from the dark web is a high-risk endeavor that carries severe legal, technical, and ethical consequences. Although counterfeit documents might initially seem attractive due to perceived convenience or anonymity, the dangers far outweigh any temporary benefits. Users face significant legal penalties, including hefty fines, criminal charges, imprisonment, and permanent damage to their personal and professional reputations. Agents often infiltrate dark web marketplaces by posing as buyers or vendors to gather intelligence on illegal activities. Undercover agents create convincing fake profiles, interact with criminal vendors, and conduct controlled purchases.
While the sheer impact of identity fraud-related costs is difficult to assess in its entirety, Javelin Research from 2021 suggests the figure is upwards of $50 billion per year for US businesses. However, with businesses losing an average of 5% of their revenue as a direct result of fraud, the true cost is far, far greater. Only by adapting to the latest fraud methods, many driven by AI, can businesses stem these losses. A multitude of components within the business model of modern-day casino operations, both person-to-person and online via apps, are attractive targets for regulatory violations, fraud, and criminal activity. The repercussions can result in costly fines, revenue loss, and even theft, impacting the bottom line and casting disparaging opinions about the integrity and security of operations. Policy makers must also address the root socioeconomic causes that drive individuals to both produce and use fake IDs.
How The Dark Web Supplies Real IDs
Once your information is out there, you will likely experience more frequent social engineering attacks and these attacks will likely include more personalized information. Organizations should conduct regular cybersecurity awareness training that includes mobile security and phishing simulation tests. Also, criminals are increasingly using databases of stolen employee mobile phone numbers to attack employer networks. If your personal information is stolen, monitor your credit report for unauthorized activity or accounts. You can also freeze your credit report for a year after you have been a victim of a data breach.
- You can also filter the results by telling Ahmia to only display links from the last day, week, or month.
- Some passports are genuine, being stolen from bona fide citizens and resold to the new identity seeker.
- Card Shops are a type of dark web marketplace that hosts the trade of credit cards and other stolen financial information.
- The solution lies in tightening up fraud detection measures and prioritizing robust age verification processes that protect not just your business but your brand’s future.
- While your IP address is hidden, the site can still collect information you share on your profile.
Banking And Financial Institutions (KYC)
Synthetic identity document fraud is now spreading at an alarming pace globally, driven almost entirely by the misuse of generative AI, experts have warned. Be sure to keep an eye out for similar promotions from other reputable fake ID websites to get the best value for your money. Onion sites are websites on the dark web that use the “.onion” top-level domain instead of “.com,” “.net,” “.gov,” etc.