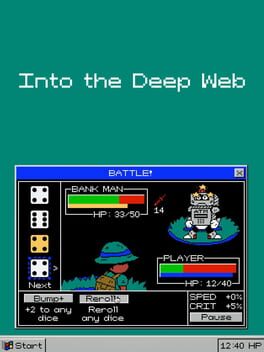
If you think the visible Internet is big enough, with over a billion websites at present, the true extent of the invisible web is beyond mind-boggling. And access exclusive content, personalized recommendations, and career-boosting opportunities. Understanding the nuances of the Deep Web is crucial in a world increasingly reliant on digital interactions. While it offers immense benefits, its potential for misuse highlights the need for vigilance, ethical considerations, and robust cybersecurity practices. These components rely on privacy and security to protect sensitive information. You can access most of the Deep Web using the same browser you use for the Surface Web.
BBC Tor Mirror
These include peer-to-peer and privacy-focused networks and can only be accessed using special tools like the TOR browser. These networks use the infrastructure of the Internet for communications, but access to them is restricted. Darknets are designed for anonymity and privacy, making them ideal for criminals to communicate and buy and sell illegal goods and services. Famous illegal marketplaces like the Silk Road are hosted on the Darknet. The deep web search sites host a vast array of specialized content, including academic databases, research repositories, private company intranets, and subscription-based services. These resources may not be readily accessible on the surface web but are invaluable for researchers, professionals, and individuals with specific interests or needs.
Exploring The Dark Web: Understanding Its Role In Cybersecurity Threats
The deep web is basically all the content that you can’t find using Google or Yahoo search. So, sites that contain a domain extension like .com, .org, .net, .biz, .info, etc. can be found on the surface web. In addition, the content on the pages don’t need any special or custom configuration to access.
Types, Viewability, And Risks Of Deep Web Content
Navigating the Deep Web exposes users to the risk of encountering malware, phishing scams, and other cyber threats. One of the most commonly known disadvantages of the Deep Web is its association with illegal activities like arms dealing, drug trafficking, and many other forms of cybercrime. The anonymity the Deep Web provides can facilitate these activities, making it difficult for law enforcement agencies to track down perpetrators. Deep web browser commonly uses robust security measures, like encryption and authentication protocols, to safeguard sensitive information. These measures enhance protection against cyber threats such as hacking and data breaches.
Accessing Dark Web Sites
From a statistical standpoint, this collective of websites and data makes up under 5% of the total internet. That leaves U.S. law enforcement in the ironic position of attempting to track criminals who are using government-sponsored software to hide their trails. For example, construction engineers could potentially search research papers at multiple universities in order to find the latest and greatest in bridge-building materials. Doctors could swiftly locate the latest research on a specific disease. Just as a search engine is simply scratching the surface of the Web, we’re only getting started.
In order to access these search engines and sites, it is necessary to use specific browsers, such as the Tor Browser. The dark web allows legitimate users to avoid censorship, but it also creates opportunities for cybercrime. The dark web’s anonymity draws users who need private communication, want to share sensitive information, or seek access to content censored in certain regions. But while it can support legitimate uses such as whistleblowing or journalistic sources, it’s also a hub for illegal activity.
Remember that illegal activities can still incriminate you, whether you are using a Tor browser. For example, you shouldn’t pirate copyrighted material, engage in terrorism, or share illegal pornography. The system is designed to provide enhanced security and privacy features. Its key features include kernel hardening, application firewall, package security, filesystem encryption, meta-proxy encryption, and binary integrity. Furthermore, it’s critical to understand that Whonix is not a stand-alone browser. It is a component of Whonix, an operating system that functions as a whole inside a virtual computer.
How Do You Access Content On The Deep Web?
This adds extra protection since opening Tor itself encrypts your traffic. A virtual private network (VPN) is a good way to mask Tor activities. It adds an extra encryption layer and passes your traffic through a secondary server of your choice, preventing anyone from seeing that you are accessing the web via Tor. While Tor offers anonymity on the dark web, your online activities leave breadcrumbs that can reveal your identity. That is why you should only use a reliable VPN like ExpressVPN or NordVPN for additional security and privacy. Many dark net sites do not undertake the necessary measures to protect users like most websites on the surface web.
Author’s Note: How The Deep Web Works
The creators assert that because their technique is so strong, even malware with root access could not determine the machine’s IP address. The only difference is that it passes your traffic through random nodes before reaching the destination. This means your activities cannot be traced or your browser history exposed. There are often copious amounts of how-to articles, software exploits, and hacked credentials for sale. Not every visitor is a criminal, but this is where most cybercrimes begin. It has a feature called CoinJoin that combines multiple coins from different users into a single transaction.
What Percentage Of The Internet Is The Deep Web?
Nowadays, many people use the Tor browser to surf the public internet and navigate the deeper parts anonymously. Another essential security feature is that all incoming and outgoing data from the app is encrypted, including any private and public keys involved. The US Naval Research Laboratory developed The Onion Routing (Tor) project in the late 90s. A network browser gives you access to sites with the ‘.onion’ registry operator. These sites are a hybrid tutorial-underground where wannabe hackers ask questions and professionals sell their services or stolen data.
Corporations and governing bodies alike currently participate in unauthorized surveillance of online activity. Some simply don’t want government agencies or even Internet Service Providers (ISPs) to know what they’re looking at online, while others have little choice. Users in countries with strict access and user laws are often prevented from accessing even public sites unless they use Tor clients and virtual private networks (VPNs).
- However, the transition to the Deep Web occurs when accessing the account using login credentials, emphasizing the interconnected nature of these digital realms.
- In a world of bulk data collection, surveillance, and personalized ad tracking, it’s up to us to take control of our personal privacy.
- The email service is available both on the surface and on the dark web.
- However, noteworthy differences exist in operation, scope, size, access methodology, applications, and security.
- In the 1990s, there were hopes that the Internet would give everyone an equal chance to access everything.
The level of safety is not the same, and the ways one can access these two webs also differ. Back in the 2000s, a study found that the deep web contained 550 billion individual documents. It’s safe to say that both these numbers grew exponentially in these 20 years of technological development. There’s also an increased chance of downloading malware, leaking credentials due to a phishing scam, or falling victim to financial fraud due to the lack of oversight. Accessing the Deep Web generally involves fewer risks compared to the Dark Web, but there are still some considerations.
Perhaps the most serious criticism of the deep web is that it undermines the openness and equality of the internet. In the 1990s, there were hopes that the Internet would give everyone an equal chance to access everything. Instead, fee-for-service sites give access to premium productivity tools only to those who can afford them. In many cases, crucial tools cost hundreds and even thousands of dollars, creating barriers to entry. Secure Communication ChannelsIn an era when cybersecurity is of paramount importance, the Deep Web offers secure communication platforms that safeguard your conversations from prying eyes. The Internet is a vast and ever-expanding network of information, connecting people from all corners of the globe.