
I also recommend covering your webcam and disabling location services before accessing .onion sites. Facebook’s official dark web version helps users access the platform in countries where it’s blocked. During testing, I confirmed it provides the same functionality as the regular site while adding Tor’s privacy benefits. The interface works smoothly, but it usually loads slower due to Tor routing. Adamant offers blockchain-based secure messaging without needing phone numbers or email addresses.
To Keep Classified Docs From WikiLeaks Secret, DOJ Drops 2 Child Porn Counts
Scientific journals often put their articles behind a paywall and charge high fees for access, but Sci-Hub offers open access to read or download research papers. While it’s a deep resource, it’s also illegal in many countries, because it may violate copyright restrictions, so check out the laws in your area before visiting. In addition to the Tor browser, you should use an antivirus program (like Norton 360) to protect your device from malware infections, and a VPN (like ExpressVPN) to secure your IP address and traffic. Also, only use .onion links from legitimate sources like The Hidden Wiki.
Aussie Cops Ran Child Porn Site For Months, Revealed 30 US IPs
Clearly, if you want to form your exclusive private club of family members, friends, fellow journalists, or other close-knit groups, Keybase is a wonderful online platform. It also works with Windows, Android, iOS, macOS, and Linux, ensuring your co-participants can use any device. This website is made public with the intention to aid the Internet users with navigation of the so called dark web.
- Since the dark web is a hidden and uncontrolled part of the web, there is a high amount of malware infections present there.
- For individuals in locations facing strict restrictions or those under oppressive governments, ProPublica is the perfect platform to share their stories.
- This makes Riseup a vital tool for people in oppressive environments or anyone concerned with online privacy.
- This dark web website offers a global version of the BBC, emphasizing international news, which is particularly valuable for those residing in areas with severe censorship.
- Outdated versions may contain weaknesses that attackers can exploit to compromise your anonymity.
That’s where dark web search engines come in — they help you discover hidden websites and make navigating this part of the internet easier. In this guide, you’ll find the top 9 dark web search engines, complete with .onion links. Each one offers unique features, such as better privacy and extensive .onion site indexing. Ahmia’s .onion link is a search engine that indexes hidden services on the Tor network, allowing users to find .onion sites safely and efficiently. It filters out harmful and illegal content, focusing on legitimate resources and services.
It’s maintained by a volunteer-run collective from the USA that protects the platform from malicious attacks and pledges to support social justice and progressive causes. Riseup’s secure email and chat help individuals communicate without fear of surveillance or data interception. DuckDuckGo is a reputable US-based software company, so their Tor site itself is safe to use.

The Psychology Of Darknet CSAM Forum Members
The system is designed to provide enhanced security and privacy features. Its key features include kernel hardening, application firewall, package security, filesystem encryption, meta-proxy encryption, and binary integrity. The creators assert that because their technique is so strong, even malware with root access could not determine the machine’s IP address. I2P, or the Invisible Internet Project, allows you to access the ordinary and dark web. Specifically, the I2P darknet is accessible, while the Tor network is accessible through the Orchid Outproxy Tor plugin.
Feds Bust Through Huge Tor-hidden Child Porn Site Using Questionable Malware
ProPublica is a popular online publication that won five Pulitzers in 2016. It aims to expose abuses of power and betrayal of public trust through investigative journalism. Since Hidden Wiki maintains all kinds of websites, ensure you don’t open something you don’t want to see. Even without monitoring your browsing activities, DuckDuckGo will offer decent answers to your questions. Purchases through links on our pages may yield affiliate revenue for us.
Haystak – Biggest Dark Web Search Engine
The dark web is used by journalists, whistleblowers, and political activists who need the protections that it offers. Anything you need to do that has to be off the books to some extent, for noble or ignoble reasons, can be done on the dark web. The website was investigated by a German police task force with cooperation from Europol and international law enforcement agencies. Yes, if you’re using tools like Tor, a VPN, and avoiding suspicious links, these search engines can be safe when used responsibly. Why does the Tor network allow such abhorrent material to remain, despite extensive opposition — sometimes even from those within these groups?
Is It Safe To Visit onion Sites On The Dark Web?
With over 15 billion records sourced from nearly 936 datasets, BreachForums remains one of the largest dark web forums for data leaks. Its escrow service and user-ranking system make it attractive to elite cybercriminals. It was created by the U.S Navy with the purpose of helping informants in foreign nations to communicate safely over the Internet. The Central Intelligence Agency (CIA), in that spirit, released a .onion site so that people from across the globe can browse their resources securely and anonymously.

Popular Dark Web Links & Websites
- While your IP address is hidden, the site can still collect information you share on your profile.
- But accessing this hidden part of the internet safely requires reliable Dark Web search engines — tools that help you explore the darknet without compromising your identity or security.
- Some popular search engines that can help you explore hidden content and anonymize your web traffic include DuckDuckGo and Ahmia.
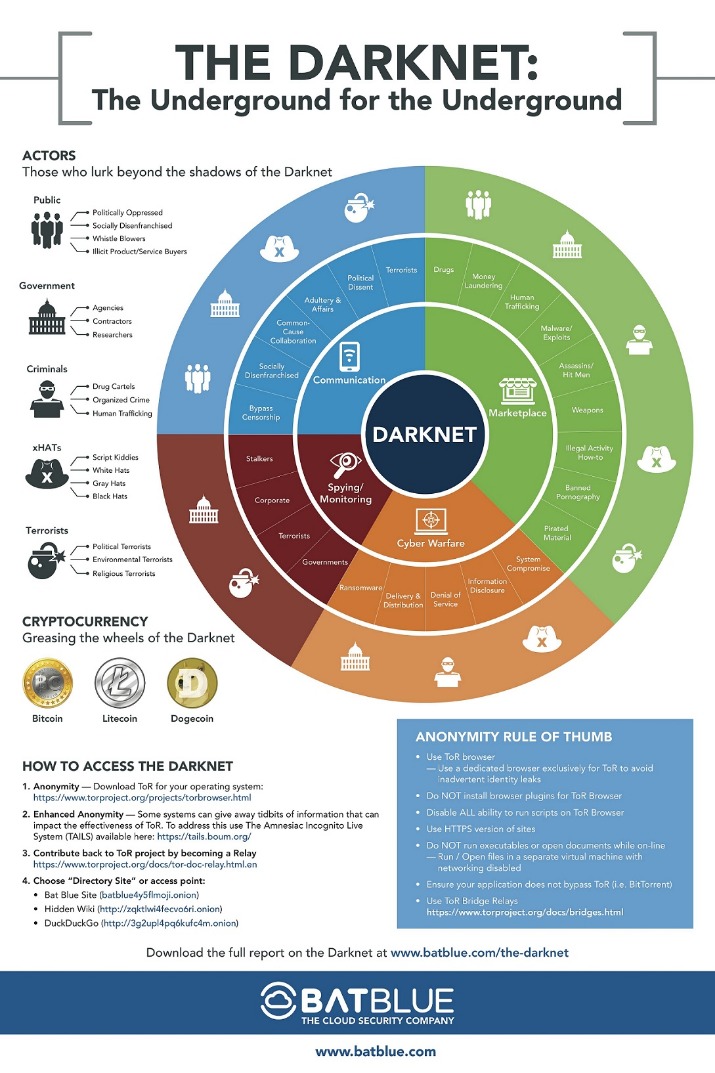
- To understand the darknet, it’s best to review how the Internet is set up.
- While they might sound the same, these websites are fundamentally different.
Surfshark supports unlimited simultaneous connections to protect as many devices as possible. Also, try its services risk-free with the 30-day money-back guarantee. A top-of-the-line VPN network that ensures maximum security while accessing dark sites online. We recommend you only visit safe dark web links to explore such as The CIA, Facebook, DuckDuckGo, and Torch. While Tor offers anonymity on the dark web, your online activities leave breadcrumbs that can reveal your identity. That is why you should only use a reliable VPN like ExpressVPN or NordVPN for additional security and privacy.
It is a reliable messaging tool where you copy/paste a text or image and send it to your addressee. It aims to advance research on terminal illnesses like cancer with access to unbiased scientific publications. Sci-Hub is a massive database that eliminates the barriers to getting scientific knowledge. It contains millions of scientific research documents from around the world. The site seeks to liberate information by making it free to individuals and institutions.
When you try to enter a .onion website, it will reroute your access request around the internet, bouncing it off three random servers before you reach the target website. This is an estimated reading time to let you know how long it will take you to read all the content on this particular PrivacyRadar.com page. Its primary focus is on delivering reliable results, allowing users to explore the dark web with fewer risks. Aside from parents uncovering activity, there are also some signs that could indicate being on the darknet.
ProPublica — Investigative Journalism On Tor
On these sites, youth will find child pornography, weapons, fake documents, drugs and even recruitment from terrorists. Now, proponents would want to point out that not all of what’s on the darknet is bad. There are forums where people can openly express their opinions without censorship, and it provides privacy to those who don’t want companies or “big brother” collecting their information.
Websites that share CSAM make this fact abundantly evident on the front page (see Supplementary Methods A.3), as well as through the use of explicit, distinct wording. How is it possible that there are so many studies classifying Tor websites and usage without addressing CSAM? A plausible explanation is that the researchers omitted the CSAM findings from their data without providing an explanation in the articles (i.e., ‘A Broad Evaluation of the Tor English Content Ecosystem13’). Many users are not just passive observers of CSAM; rather, they are sexually motivated6. Previous research has suggested that problematic use of legal pornography can escalate to violent sexual behaviour and the use of CSAM.



