This channel claims to offer the best logs in terms of price-to-quality ratio and provides daily updates with over 2,000 fresh logs per day. It aggregates logs from various sources, including those stolen using LummaC2 and Stealc malware. Despite these changes, many cybercrime-related Telegram channels remain active and influential.
These forums are typically dominated by a small group of experienced members who share a range of illicit resources (Afroz et al., 2013). Consequently, many cybercriminals have turned to alternative platforms such as social media, which provide a more dynamic, decentralized environment for exploiting vast user bases while evading traditional security measures (Elezaj et al., 2021). In Blackhat Resources channels, users frequently engage with the content by providing feedback on the effectiveness of various hacking tools. They share both positive and negative experiences, which helps other members make informed decisions about which tools to use. For instance, a user commented, ”i was not able to download it before,” indicating a problem with a specific tool, while another might say, ”Try method 1 or 3 I hope REMCOS working,” suggesting effective methods.
Print + Premium Digital
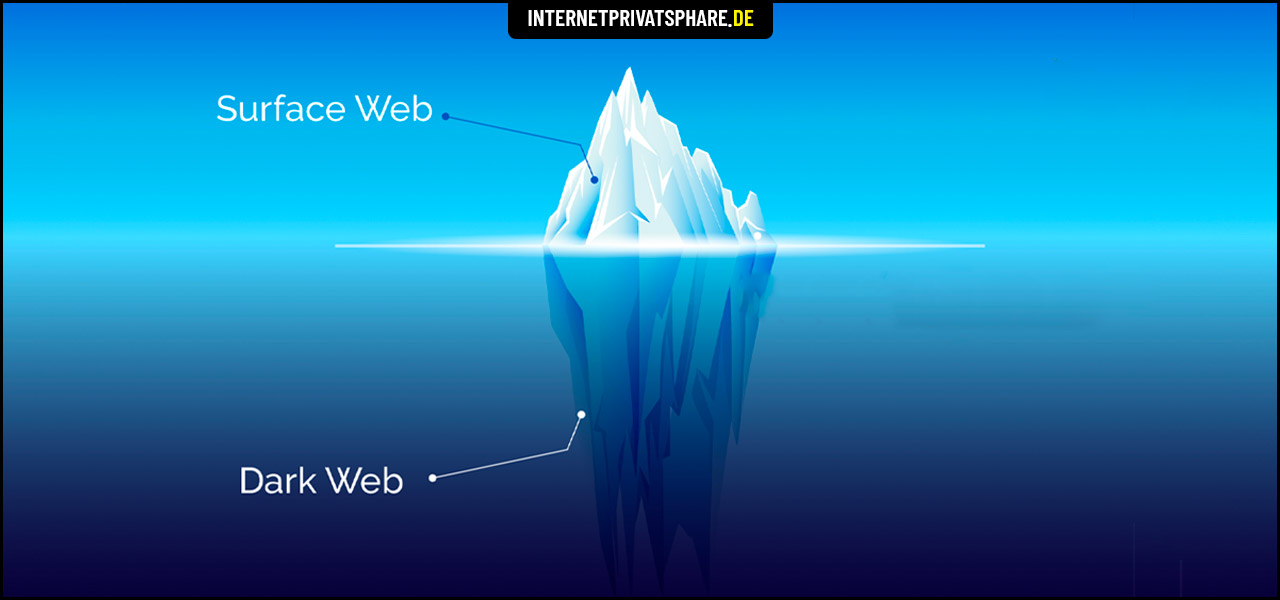
This also allows Telegram’s users to utilize features such as self-destructing messages, so called “secret chats,” and groups which the platform’s visitors can access anonymously. That is partly why these groups are often referred to as Telegram’s “dark web” channels. The dark web is the intentionally hidden part of the internet accessible only through specific tools, such as Tor (The Onion Router) browser or the I2P (Invisible Internet Project).
DarkGram: Exploring And Mitigating Cybercriminal Content Shared In Telegram Channels
By being aware of these threats, users can take necessary precautions to protect themselves and their sensitive information while using Telegram. Another important factor is how Telegram offers hacking groups and lone wolf actors a way of hardening their operations. Having to register a domain to offer services and tools for sale makes threat actors’ operations vulnerable to distributed denial of service (DDoS) attacks that can take them offline. Telegram channels bypass this requirement for a domain and ensure cybercriminals can stay online as long as the Telegram service remains online.
Most Viewed Posts
- After reviewing the complaint, we will remove this Telegram channel from the search.
- Dark web Telegram merely refers to groups and channels that host illicit content—much of which originates from the dark web—or contain shady characters who want to steal your personal information or trick you into signing up for fake NFTs or crypto schemes.
- While Telegram remains a critical hub for cybercriminal activities, it is just one part of the larger dark web ecosystem where threat actors exchange stolen data, hacking tools, and illicit services.
- Users learn from each other’s requests and feedback, experimenting with different approaches to boost their social media presence.
- Browser fingerprints are unique identifiers that can be used to track users’ online activities and potentially compromise their privacy.
Unlike dark web forums that often require specialized software, specific configurations, or encrypted networks, Telegram can be easily accessed through a standard internet connection and a smartphone or computer. This simplicity in technical requirements means that users do not need to go through the hassle of setting up complex systems or acquiring specialized tools, which further contributes to the accessibility of Telegram. In this section, we will explore the topic of Telegram and its easier accessibility compared to dark web forums.
Man Threatens To Sue Pharmacy After Prescription Mix-Up Exposes His Affair
Users have found the app to be a convenient medium for buying and selling illegal goods, from drugs to stolen credit card information. The platform’s structure, which supports anonymous group creation and minimal oversight, facilitates these transactions 2. By joining specialised groups, users can discreetly exchange illegal items, highlighting the platform’s role in enabling covert trade operations. The ease with which users can access these groups underscores the app’s function as a digital marketplace for illicit activities. Unlike more specialized cybercrime groups, EMP/mailpass/sqli Chat covers a broad range of topics, including stolen account sales, financial fraud, SQL injection techniques, and malware deployment.
Breached Data
In today’s fast-paced digital landscape, it’s essential for businesses to find innovative and cost-effective ways to reach their target market. As a tech enthusiast, staying up-to-date on the latest trends, news, and innovations in the industry is crucial. “At the heart of this case is the lack of moderation and co-operation of the platform, in particular in the fight against crimes against children,” said Jean-Michel Bernigaud, the secretary general of French child protection agency Ofmin, on LinkedIn. Not doing enough to police child sexual abuse material (CSAM) is one of the chief allegations from French prosecutors. On Wednesday, the BBC learned that while Telegram does respond to some takedown requests from police and charities, it is not participating in programmes aimed to proactively prevent the spread of images and videos of child sexual abuse. Pavel Durov has been charged for suspected complicity in allowing illicit transactions, drug trafficking, fraud and the spread of child sex abuse images to flourish on his site.

Top 6 Dark Web Telegram Groups And Channels

Most Telegram channels including illicit communities can make criminal activity on the platform more accessible and easier for even low-level cybercrime. The proliferation of cybercrime on the internet has given rise to thousands of criminal communities. These corners of the internet, often dominated by malicious actors, allow them the space to coordinate and carry out their illegal activities successfully.
Parallels Between Dark Web Forums & Illicit Telegram Communities
There has been some migration, but so far only Signal seems to have benefited from the crackdown on Telegram. It is important to note, however, that criminals don’t stick to just one platform. Most criminals appear to be using Telegram as well as other messaging apps, and in fact they may change their messaging app depending on the data they are sharing. The presence of such a channel highlights how stolen financial data circulates within dark web markets, making Telegram an essential tool for cybercriminal activities. To mitigate the risks posed by exposed credentials, organizations must actively monitor and respond to identity-related threats. SOCRadar’s Identity & Access Intelligence module enables security teams to detect compromised credentials across various dark web sources, including stealer logs, data breaches, and underground Telegram channels.
- This tool enables users to launch scalable DDoS attacks with minimal technical expertise.
- These SMM panel links were frequently shared in cybercrime forums, displaying consistent patterns across websites that provided multiple services for various social media platforms.
- Additionally, Omega Cloud maintains a database exceeding 2 billion records, accessible through a subscription-based model.
- In contrast, blackhat resource channels contributed only 87 phishing URLs, as users here tend to have higher technical knowledge and are more vigilant.
- A file was considered malicious if detected by Hybrid Analysis and also had at least two antivirus scanners flagged it.
Our study offers a comprehensive overview of coordinated cybercriminal activity on Telegram, showcasing the wide range of tactics employed across different Cybercriminal Activity Channels (CACs). It also paves the way for future research solely dedicated to each CAC category, as the unique strategies and engagement methods merit deeper exploration to uncover more nuanced insights and inform targeted interventions. By open-sourcing our dataset and the DarkGram model, we provide a valuable foundation for continued investigation and collaboration in the fight against cybercrime. With over 500 million active users, Telegram provides a large pool of potential targets for cybercriminals. This diverse user base not only increases the chances of successful scams and frauds but also allows cybercriminals to target specific demographics or geographical locations. Additionally, Telegram has minimal technical requirements, making it accessible to a broader audience.
Thematic Analysis Of Replies
However, it has also allowed numerous dark web forums and other nefarious groups to move onto the messaging app as well and create illicit channels successfully. More recently, there has been a spike in illicit activities moving into online messaging applications like Telegram. Combined these two facets of cyberspace host a plethora of criminal activities carried out by threat actors. Beyond system exploitation tools, several tutorials focused on promoting social engineering tactics (other than phishing).
PureVPN is the best-in-class VPN that not only provides you with digital freedom but also takes care of your digital security when you are browsing the web. Dark web is not safe to browse without a VPN, as it leaves traces of your identity. Take a first step towards your digital security with PureVPN 7-day free trial and secure yourself while accessing dark web anywhere. All transactions are conducted through cryptocurrency payments, with coordination handled via Telegram contacts. Although its Telegram channel was previously taken down due to policy changes, the group has successfully reestablished its presence and continues its operations.
WEIRD MEMES🥥 Telegram Channel
Primarily focused on DDoS attacks, Dark Storm Team follows an opportunistic targeting strategy across various sectors. In addition to its cyber operations, the group also promotes hacking services for hire through its Telegram channel, offering DDoS attacks on protected websites and database dumps from organizations such as banks and airports. The landscape of cybercrime has evolved dramatically, with hackers leveraging both dark web forums and illicit Telegram communities to facilitate their activities. While there are many parallels between the criminal activity between illicit Telegram groups and dark web forums, there are several key differences between these communities as well. These illicit communities also allow countless users to have more anonymity within a global community that allows them to share, trade, or make money selling services or exploits successfully.
In many cases threat actors have moved directly off of more traditional TOR websites, and onto Telegrams offering the exact same goods and services. Although cybercriminals mostly use a combination of messaging apps, Flare’s research shows that as of January 2025, Telegram is still the most-used communication tool among threat actors. Groups used password-protected channels to trade exploits, stolen data, and malware kits. But as operations scaled, IRC’s static architecture and lack of mobile adoption left it vulnerable. The torch passed to dedicated darknet forums, often on the Tor network, which allowed marketplaces and vendor reputation systems to emerge.