There is no shortage of methods to get hacked, but there are just as many ways to defend against it. By following these suggestions, you can deter unwanted intruders from accessing your accounts at home or work. While no information is stolen during a DDoS attack, it can be used for extortion or to conceal other hacking activities. A Distributed Denial of Service (DDoS) attack is designed to disrupt access to websites and other internet resources.
Run Antivirus/Anti-Malware Software

It is crucial for individuals to remain vigilant in protecting their personal information and for organizations to prioritize robust security measures to prevent data breaches. Only through collective efforts can we hope to combat the dark world of fullz and safeguard our identities in the digital age. Beginning in September 2021, Abacus Market has established itself as one of the leading dark web marketplaces. After AlphaBay closed, Abacus Market took its place as the world’s largest underground darknet marketplaces.
Journalism: SecureDrop Keeps Evolving
This typically includes data such as the victim’s name, address, date of birth, Social Security number (or equivalent), email, phone number, and payment card details (including CVV codes), and bank account information. Although dark-web marketplaces utilize technologies like Tor and I2P to enhance anonymity, these methods are not foolproof. Law enforcement agencies continuously improve their ability to trace transactions and monitor marketplace activity.
PayPal Account Or Card Cancellation
Shortly after the breach, a hacker group known as USDoD listed this data on dark web marketplaces, pricing it at a staggering $3.5 million. Cybercriminals are always on the lookout for new ways to use stolen credentials for generating income. And because people regularly store sensitive personal information across various online accounts without taking the extra measures needed to protect that information, cybercriminals have plenty to work with. Plug one hole, one exploit, and fraudsters will focus their efforts on a different one.
AlphaBay debuted in September 2014 and quickly eclipsed Silk Road’s record, amassing more than 200,000 users, 40,000 vendors and 250,000 illicit listings. The FBI, DEA and international partners infiltrated the site during Operation Bayonet. On July 5, 2017, Thai police arrested founder Alexandre Cazes; a week later he was found dead in his Bangkok cell.
Set Up Tor Browser
Use of fullz by bad actors presents a risk to businesses who allow for digital identity verification, as fullz give fraudsters a deep ability to impersonate a legitimate customer. Typically, fullz are most valuable on dark web markets, and useful to threat actors, when they include payment information and logs (See Figure 1). They are commonly utilized to cash out money from the victims’ accounts, as the complete PII in possession of the threat actor can be exploited to bypass online banking verification processes. Leaked credit cards from Telegram channels account for the overwhelming majority of compromised payment card details. B1ack Stash’s primary motive from the outset has clearly been financial gain, which they have pursued by building a strong reputation as a card seller within the carding community.
Shifts In User Behavior And Marketplace Structures
As with credit cards, the location of the victim whose information is up for sale has a significant influence on price. Japan, the UAE, and Europe have the most expensive identities at an average of $25. Due to limited data on credit cards from other countries, we were unable to adequately compare prices for credit cards from different places.
2FA requires that users have access to an email or device where the identity verification request can be sent. 2FA is a powerful deterrent against fraud, but it only works if you already have contact information for a particular individual. Truly sneaky fraudster can also sometimes move the victim’s phone number to a phone they control, where they can receive 2FA codes. Fullz might mean that a criminal has access to the ID number and social security number, but rarely do they have access to the physical ID of the identity theft victim. So by requiring a photo of the front and back of the ID, you’ll be creating a major speed bump for fraudsters who thought they could get away with just entering information as plaintext.
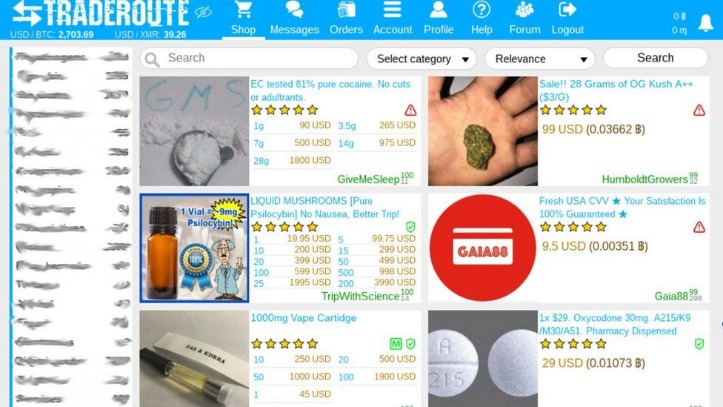
Marketplaces
Fullz are usually pricier than the standard credit card credential, but still tend to cost less than $100 per record. Fullz can be cashed out (turning credentials into money) in various ways, including performing bank transactions over the phone with the required authentication details in-hand. This first blog looks at developments on dark web forums and marketplaces in 2023. This year was a turbulent one for dark web marketplaces, with some of the major players falling into extinction either as a result of law enforcement action or by their own volition. But first we’ll look at cybercriminal forums, where there was a flurry of activity thanks to the disruption of BreachForums (which continues, cockroach-like, in spite of some major hiccups). Fullz, consisting of complete PII sets, are highly valued on the Dark Web as they more easily enable identity theft and fraudulent activities.
These breaches can occur at large corporations, government agencies, or even small businesses with weak security measures. Once obtained, the stolen data is compiled into fullz packages and sold on underground marketplaces. Fullz are often used for identity theft, account takeovers, loan fraud, or other financial scams. The availability of fullz on dark web marketplaces and forums poses significant risks to individuals and businesses alike. The Dark Web Hub equips law enforcement, enterprises, MSSPs, and researchers with essential knowledge to navigate dark web threats. Our continuously updated content provides in-depth insights into marketplaces, ransomware actors, and hacking forums, helping you stay informed and proactively address challenges to safeguard your organisation or community.

This move is likely to increase the platform’s popularity and draw in new customers. B1ack is notorious in these forums for distributing CCS/FULLZ—credit and debit cards along with full personal information, known as “FULLZ,” which contains enough data to commit identity theft or fraud—as freebies. Further investigation indicated that B1ack started this marketing campaign in January this year by posting hundreds of free stolen payment cards to build credibility and attract more customers. The dark web, by contrast, is a deliberately hidden subset that requires specialized software such as the Tor Browser or I2P to reach. Instead of standard URLs, it uses non‑indexed domains like “.onion” and routes every connection through multiple encrypted relays to mask both server and user identities. That anonymity empowers political dissidents, whistleblowers and investigative journalists, but it also shelters ransomware gangs, contraband markets and extremist forums.
- Scammers on darknet markets claim to offer legit tools or services, but instead provide you with malicious software that can infect your device.
- Stolen credit cards are used to cash them out or make purchases that can be resold.
- But first we’ll look at cybercriminal forums, where there was a flurry of activity thanks to the disruption of BreachForums (which continues, cockroach-like, in spite of some major hiccups).
- By following these suggestions, you can deter unwanted intruders from accessing your accounts at home or work.
Regular audits and compliance with standards like the Payment Card Industry Data Security Standard (PCI DSS) are also essential to maintaining secure systems and practices. One of the earliest and most notorious dark web marketplaces was the Silk Road, which paired the darknet with Bitcoin for anonymous transactions. Its success set the standard for other marketplaces to follow, leading to the rise of a vast and shadowy underground economy. As these marketplaces evolved, so did the challenges for security professionals, who now face a constant battle to keep up with ever-changing tactics used by criminals.
Want To Find Out More About Hacking Forums, Dark Web Marketplaces, And Autoshops? Visit Our DARK WEB HUB
Operational security, or OPSEC, is the discipline that turns technical anonymity into real‑world protection. Tor and VPNs mask your network path, but a single careless click can still expose your identity. Internet shutdowns affected 4.78 billion people in 2024 alone, as governments from Iran to Myanmar throttled access during protests and elections. In that climate, the dark web’s anonymity tools serve as a digital lifeline for journalists, whistleblowers and ordinary citizens who need uncensored information. The surface web is the portion of the Internet that traditional search engines such as Google, Bing and DuckDuckGo can crawl and index.
This solution focuses on identifying stolen data, brand misuse, and potential threats before they can cause significant harm. With Brandefense, businesses gain early visibility into risks that may otherwise remain undetected until it’s too late. Fullz is fraudster speak for financial information that includes the full information of the victim, including name, address, credit card information, social security number, date of birth, and more. As a rule of thumb, the more information you have on your victim, the more money you can make off of those credentials.
- When he’s not empowering PrivacySavvy’s readers to take control of their online security, Saheed enjoys distance running, playing chess, and exploring the latest open-source software advancements.
- This includes opening new credit card accounts, applying for loans, filing false tax returns, or even committing medical identity theft.
- This has prompted some predictions about the “death” of dark web forums, though he said that’s premature.
- Vice City listens to the problems faced by its customers and vendors and solves them so that they can keep using the platform with ease.
- “Fullz” is a slang term used on the darkweb by individuals selling information obtained from data breaches.
For businesses and individuals alike, understanding these threats is the first step in securing their digital assets. However, combating dark web risks requires more than just awareness—it demands proactive and comprehensive protection. With advanced dark web monitoring, threat intelligence, and brand protection services, we help you uncover hidden dangers, prevent data breaches, and safeguard your reputation. Our platform ensures that your brand stays one step ahead of cybercriminals, giving you peace of mind in an increasingly complex digital landscape. Explore how Brandefense can empower your brand to thrive securely, even in the shadow of the dark web. Dark web monitoring platforms, such as Lunar, provide an automated solution to safeguard personal identifiable information (PII) and credit card details.