While some studies have claimed that illegal Bitcoin activity is as high as 44%. Simply accessing the dark web and using the Tor browser may already raise government suspicion. Anyone can access the dark web, and it’s not that complicated to do so. Just remember, if you want to explore the dark web, be very careful. This allows you to use the computer without the risk of corrupting your computer’s normal operating system with viruses or malware. Tails also protects you from possible malware, viruses, or keystroke loggers that may have already infected the computer, as it doesn’t run the operating system already installed on the device.
- Every search engine uses bots to crawl the web and add the new content they find to the search engine’s index.
- For a web page to be on the surface of the web, such as on Google search engine result pages, a web crawler must first crawl and index it.
- If you use Tor to access the dark web or unblock websites, connect with a VPN for extra security.
- Users leverage these platforms to organize protests, whistleblow, share survival guides, or share files P2P.
- Lots of .onion sites contain very nasty things, and many of them are likely scams.
- It relies on P2P connections and requires specialized tools and software.
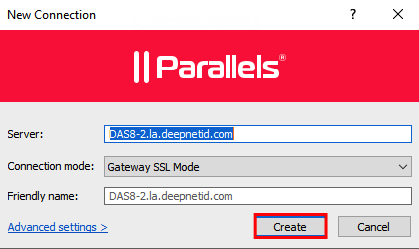
Our Network

Whether for professional or personal use, accessing the deep web responsibly ensures privacy, security, and efficiency. You can also use security tools with AI-powered scam detection capabilities to identify and block suspicious links and websites in real-time when browsing the dark web. You should consider using data breach monitoring tools to regularly check if your personal information has been leaked onto the dark web. Also, be wary of RATs (Remote Administration Tools) that malicious actors might try to install through dark web sites to gain control of your system. This is the main way that search engines become aware of a certain website or web page, and is generally how sites like Google add web pages to their index. If the signal goes through the Tor network first, your ISP will be able to see that you are attempting to connect to a Tor node.
onion URL Structure
NordVPN’s NordLynx protocol is more than secure, with a certified no-logging policy that guarantees no logging and storing of your sensitive data. Because of this, not many people are willing to give it a shot except if they have a very good reason. If you’re one of them, good luck finding a provider that supports it.
WANT TO TRY THE TOP TOR VPN RISK FREE?
You will find paywalled news articles, subscription sites, and private social media posts all live there. It’s not some shady underworld (that’s the dark web, which is a whole different thing). It’s just the part of the web that’s locked behind passwords, paywalls, or privacy settings. Perhaps the best-known thing you can buy on the Dark Web is information collected in what seems like the almost daily data breaches we read about in the news.
Deep Web Search Engines & Browsers
- However, it’s illegal if you venture into the dark web to commit unlawful actions such as downloading child porn, buying fake documents, drugs, credits card, and more.
- You can also search Google Books, which contains extra information you won’t find in Google.
- The dark web is a section of the Internet not searchable through traditional search engines, where privacy and anonymity reign.
- If you’re intrigued and want a firsthand experience, follow this guide to learn how to access the deep web with an anonymizing browser.
First, it’s difficult to track and monitor activity on the dark web since much of it is encrypted. Many dark websites are perfectly legal and safe to use and, in many cases, are better for your privacy than clear websites. Alternatively, users can connect in opennet mode, which automatically assigns peers on the network. Unlike darknet mode, opennet uses a handful of centralized servers in addition to the decentralized peer-to-peer network. A VPN allows a user to encrypt all internet traffic traveling to and from his or her device and route it through a server in a location of that user’s choosing.
Tor Over VPN (Recommended)

Tor is a Firefox-based browser made specifically to enable access to onion sites, hence the name The Onion Router. This browser, on paper, ensures anonymity by routing your traffic through different “secure” nodes, preventing tracking and surveillance. Later in our guide, we’ll see why this isn’t ideal for browsing the dark web safely. The dark web contains content that’s only accessible through networks like Tor.
NordVPN — The Best VPN To Access Content On The Deep Web Safely
Instead of relying solely on HTTPS, you can verify site authenticity through multiple trusted sources, such as official PGP signatures or well-known directories. Another problem with this system is that there’s increasing evidence that law enforcement agencies — such as the FBI — run and operate large number of exit nodes. This means that if you do anything illegal on the dark web and are unlucky enough to be routed through one of these nodes, the authorities will be well aware of what you’re doing.
Do I Need A VPN If I Access The Dark Web On My Phone?
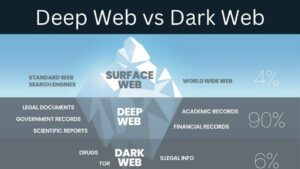
Many internet service providers (ISPs) and governments are suspicious of Tor use, but a VPN will hide your internet activity and help prevent anyone from knowing that you’re using Tor. The websites you visit every day aren’t all there is to see on the internet — not even close. Beyond this “surface web” is the deep web, and within the deep web is the dark web. Then, use data breach monitoring software to help find out if your personal data has leaked onto the dark web. If you want to view archived content (pages or whole websites that are no longer “live” online), the Wayback Machine stores older versions of many websites.
Deep Web Vs Dark Web Vs Surface Web
Unfortunately, the dark web is also where underground marketplaces flourish, selling drugs, weapons, stolen IDs and credit cards, and other ill-gotten goods. It is also used to facilitate human trafficking, money laundering, and worse. The dark web is a refuge for information leakers and whistleblowers.
For those who have endured harm at the hands of others, they may not want their attackers to discover their conversations about the event. If an activity is deemed illegal by the governing bodies you fall under, then it would be illegal. Which dark web browser did you use to visit sites on the dark web?
Moreover, malicious actors can attempt phishing scams to steal your data and identity for extortion. Nowadays, many people use the Tor browser to surf the public internet and navigate the deeper parts anonymously. Another essential security feature is that all incoming and outgoing data from the app is encrypted, including any private and public keys involved. Think of Tor as a regular browser like Firefox, Google, or Safari.
Keybase also offers extremely user-friendly secure chat and file-sharing services through its app. One of the most popular ways to get around the dark web is not to use a search engine at all. Just like in the old days of the internet, the dark web maintains numerous indexes of sites, like The Hidden Wiki. Unlike Ahmia and Haystak, however, DuckDuckGo doesn’t search .onion sites.