As I’ve previously said, it’s a good idea to keep your interactions with the dark web to a minimum, unless you can absolutely trust the people you’re dealing with. You’ll often see a sign in stores that says “look, don’t touch,” and it’s not a bad adage to bear in mind as you navigate around the dark web. The dark web, for the uninitiated among you, is a virtual neighborhood beyond the borders of the normal, everyday internet (which includes the website you’re looking at right now). It’s somewhere Google and Bing don’t index, and you need special tools to get to it. However, the technology that Yippy manages, was created in Carnegie Mellon. In addition, this included the acquisition of an unlimited license for the software known as Vivisimo’s Velocity, acquired by IBM in 2012 and renamed IBM Watson Explorer.
The Best Dark Web Links — Safe & Verified Sites In 2025
Nonetheless, if whatever you do is deemed illegal in your country, you can get into trouble. Nowadays, many people use the Tor browser to surf the public internet and navigate the deeper parts anonymously. Therefore, the legality of the dark web will mainly depend on how you use it. You can quickly get into trouble for acting illegally, such as infringing on other people’s safety and freedom. The creators assert that because their technique is so strong, even malware with root access could not determine the machine’s IP address.
Explicit And Illegal Content
Stopping their growth takes serious effort from US agencies like the FBI, often working hand-in-hand with international law enforcement. The buyers, or “consumers,” are cybercriminals who use these tools to launch illegal activities. The victims, who are common users, businesses, and even banks, who end up paying the price. Just like on the regular internet, phishing is a big problem on the dark web as well. Fraudsters create fake versions of popular darknet sites to trick users into entering login details or personal data. If you fall for it and log in, they immediately steal your credentials and either sell or use them for other scams.
A What Are Onion Websites?
You need to register first to purchase products from this marketplace. Vice City Market is a new and cutting-edge dark web marketplace where you can find a range of products and vendors at an affordable price (compared to the damage they do to the victims). To access this marketplace, you must register, but before that, you must verify yourself as a human by passing a CAPTCHA test. The browser uses onion routing technology to route the internet traffic through multiple relay nodes that provide layered encryption. The layers of encryption hide your data and activity from snooping eyes. As these marketplaces keep changing, it is critical to stay on top of the main platforms on the dark web worth monitoring.
Key Features Of Brandefense’s Dark Web Monitoring Solution
Tor is like the public-facing door to the dark web, and there are even mobile apps for Android and iOS. Not Evil is a reflection of what the community is looking for and what the community reports as abusive or inappropriate content. On April , the Genesis market was seized as part of the international law enforcement crackdown dubbed “Operation Cookie Monster”. The site had specialized in the sale of “browser fingerprints”.
Finding A Silk Road Alternative: What Are The Best Options Today?

It sells stolen card data — dumps, CVVs, even wholesale batches — and lets users bid on fresh leaks. Despite multiple takedown efforts by law enforcement and security researchers, Brian’s Club has resurfaced repeatedly and continues to add new stolen credit card data. Abacus Market is one of the newer darknet marketplaces that quickly filled the gap left by AlphaBay’s takedown. It hosts over 40,000 listings and offers everything from illicit goods and substances to hacking tools. With an estimated market value of around $15 million, it has grown into a massive hub for cybercriminal activity. The marketplace has an intuitive interface and offers powerful search tools that make it easy for you to find products from both local and international sellers.
The Hidden Wiki
- Bear in mind too that laws about freedom of speech and censorship vary from country to country, which is part of the reason the dark web exists in the first place.
- These lists are curated based on user feedback, uptime, and overall reputation, making them indispensable tools for navigating the darknet landscape.
- Because it’s a members-only platform, you’ll need to register first.
- It also offers works of art, course material, and audiobooks for download.
While many dark web websites, like the former black market website Silk Road, are used to facilitate criminal activity, there are also plenty of legitimate dark web websites. ProPublica is a non-profit, Pulitzer Prize-winning news outlet that focuses on abuses of power and issues of public trust. ProPublica’s investigative journalism can upset powerful interests, so the outlet joined the dark web to help their journalists and readers access their content anonymously.

Venus crawls and gathers a wide array of onion sites, ensuring you have access to the latest information available on the dark web. The search engine doesn’t impose censorship, meaning you can find a broad spectrum of sites, including those that may be illegal or disturbing. Other dark web search engines worth investigating are Ahmia, Torch, NotEvil, and the Onion URL Directory—just type out some keywords for what you’re looking for. Some of these sites can be found through regular web browsers, but you’ll then need to switch over to Tor once you’ve got the onion links you want to follow. It’s a part of the internet that’s less regulated and more shadowy, for better and for worse. Ahmia developers believe that the Tor network is an important distributed platform to protect anonymity and privacy around the world.
In 2022, for example, BidenCash was linked to the breach of over 1.2 million credit card records. Since its inception, the market has catered to criminals looking for high-quality counterfeit items, such as fake IDs, passports, and branded luxury goods. One of the distinguishing features of Fresh Tools Market is its focus on providing up-to-date, freshly obtained tools and credentials. FreshTools, founded in 2019, specializes in selling stolen account credentials and data, particularly webmail, RDPs (Remote Desktop Protocols), and cPanels. Mega Market, established in 2016, experienced a surge in popularity following the takedown of the Hydra market. Launched in 2021, Abacus Market caters primarily to English-speaking users.
Pro Tip: Use A VPN To Stay Safe When Using The Dark Web Search Engines
With ZeroBin, you can easily exchange encrypted messages within the dark web. With 256-bit AES encryption, this platform enforces its two-fold service of secure messaging and zero logs of your activity. This is largely due to harmful elements in the dark web, and Ahmia contains certain questionable and largely illicit links. Therefore, use NordVPN to view search results and browse anonymously. In addition, Haystak offers a premium plan that allows deeper search, email alerts, and access to historical content. Few countries operate with strict censorship on citizens’ internet access, preventing them from getting information in or out.
Explore The Dark Web More Securely With A VPN
You can archive any site you want, or retrieve historical records wherever available. In today’s digital era, where information is constantly on the move across all digital platforms, an… It is a relatively new provider but offers better features than most established VPNs.
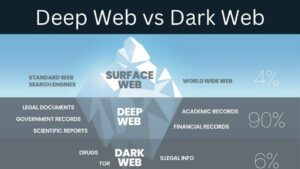
- The deep web is made up of email platforms, workplace portals, subscription services, and banking websites — basically anything that requires a login.
- Torch is one of the oldest and most popular onion search engines on the dark web, serving over 80,000 requests per day.
- SecureDrop is a secure hub for journalists and whistleblowers to interact and trade vital information.
- BidenCash became known for regularly leaking huge amounts of stolen credit card data and personal information — often for free.
- In April 2016, its APIs were compromised, resulting in stolen messages.
Plus, it’s slower since your data travels through the same four steps – entry node, relay node, exit node, and then the VPN server. As we mentioned above, when you connect to Tor your data first goes through an entry node, which can see your IP address. By connecting to a VPN before using Tor, you mask your real IP address before it reaches this entry node, adding an extra layer of security and anonymity. Your activities on the dark web are not entirely shielded from tracking, and relying solely on anonymity can lead to a false sense of security. The dark web draws not only serious cyber criminals but also law enforcement agents aiming to catch them.
The Imperial Library currently holds around 1.5 million books, some of which may be hosted illegally, and thus, their consumption might violate copyright laws. To protect yourself against any legal repercussions, you should consider using NordVPN. Proton also offers other security tools besides ProtonMail, such as Proton Drive, Proton Pass, Proton Calendar, and Proton VPN. In addition, you can connect your Keybase account with X, GitHub, or Reddit to let people easily trust that they are talking to the actual person.