Though no one should bat an eye just because you’re attempting to access the dark web, keep in mind that in some countries, like the United States, even a simple foray can get you in trouble. Well, VPN over Tor is basically its opposite – instead of going through the VPN first, the signal passes through the Tor network, before going through the VPN. Next step – your request will be transferred to Tor entry nod which in turn transfers to one or more Tor relays.
Use Additional Security Tools
This service is a good source of statistics if you have a school project requiring research on Tor and the dark web. However, note that the site only uses non-sensitive and public data for the metrics. The Tor Metrics is a good place to get more information about the Tor project. It collects data from the public Tor network and archives historical data of the Tor ecosystem. SecureDrop is a dark web link that allows whistleblowers on the dark web to communicate and share information with journalists safely and without being tracked. It may initially look abandoned, but the community members will answer your questions.
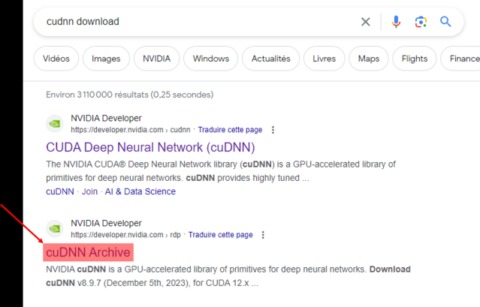
How To Find New, Active Dark Web Links
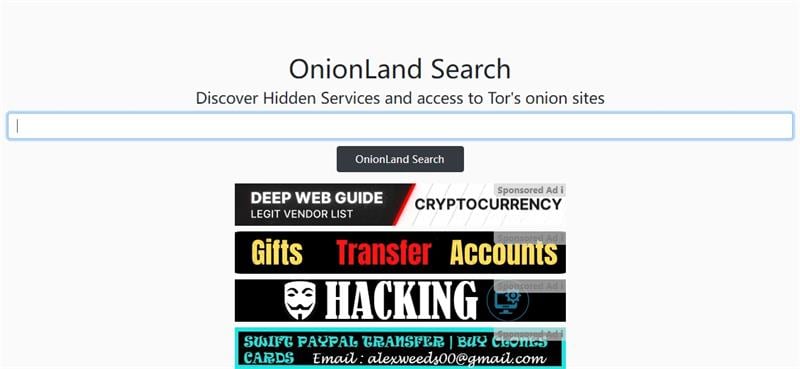
The users only have access to a fraction of the available data and web pages. Dark web search engines exist, but even the best are challenged to keep up with the constantly shifting landscape. The experience is reminiscent of searching the web in the late 1990s. Even one of the best search engines, called Grams, returns results that are repetitive and often irrelevant to the query.
Are Dark Web Search Engines Used By Law Enforcement?
With an index boasting over 100,000 web pages, including various Dark Web marketplaces and forums, Candle caters to users seeking diverse content within the hidden corners of the internet. Instead, download Tor, the most secure and user-friendly option for accessing .onion sites. Despite some skepticism about its origins and privacy due to its military development, Tor remains the preferred choice for safe dark web navigation. This part of the internet is notorious for illegal activities, facilitated by the anonymity it offers. Crimes range from data theft and selling illegal goods for cryptocurrencies to human trafficking and more severe offenses.
BBC Tor Mirror
- Like the other dark web search engines, Candle doesn’t track user activity or store data, giving users peace of mind about their online activities and anonymity.
- That’s why many search engines have been developed specifically for this space.
- Instead, download Tor, the most secure and user-friendly option for accessing .onion sites.
- It does have sponsored listing at search result page like other search engines but it brings a ads-free homepage to you.
- Each section includes a robust overview, expanded Key Features, Use Cases, Limitations, Real-World Examples, and Personal Take, plus the web address for each engine.
Watch for unexpected changes in system performance that could indicate malware. Cryptocurrency miners and other malicious software often target dark web users. Using a reliable antivirus to scan your device is worthwhile if you spot suspicious spikes in system resource usage. Always run the latest version of the Tor Browser to protect against security vulnerabilities. Outdated versions may contain weaknesses that attackers can exploit to compromise your anonymity.
What Is Burp Suite And How Is It Used For Web Application Security Tes
Tor updates, like V3 to V4 onion transitions, improve security but may deprecate older .onion addresses, forcing engines like Haystak to reindex and update support. This enhances privacy against attacks but causes temporary downtime or broken links. This enhances security but requires users to verify via trusted sources like r/onions, tor.taxi, or DuckDuckGo. Keep an encrypted offline list of updates to maintain access without interruptions. They support targeted searches for corruption data or censored news, with features like Ahmia’s API for automated workflows. Use them with PGP encryption for secure communications and Tails OS to isolate sessions, ensuring sources remain protected in high-stakes environments.
Why Security Leaders Prefer To Buy CTI Solution For SaaS Platforms In 2025
Torch is designed specifically to access a large volume of general .onion websites. Ahmia, in contrast, is a traditional web search engine compatible with the Tor network and filters out unsafe and illegal content when used for dark web navigation. This deep web search engine can be accessed via the surface web and Tor.
Also, there’s a vast amount of unsavory content on the dark web, as well as a significantly high number of hackers and scammers looming on the platform. This allows you to use the computer without the risk of corrupting your computer’s normal operating system with viruses or malware. You can either sell or buy goods on the dark web, but both present difficulties. The dark web is also a place for scammers to attract vulnerable and unwitting victims.
The invisible web is made up of data and information that is not indexed and cannot be searched for by using traditional search engines. It includes media and archives which cannot be crawled and indexed with current search engine technology. While some .onion sites provide essential services like secure communication and censorship-free journalism, others spread malware or run scams. With this in mind, finding verified links is crucial for avoiding threats on the dark web. The deep web consists of anything online not indexed by standard search engines, such as personal email accounts, online banking, private databases, and subscription-only content. While the deep web is hidden from public view, it is not inherently malicious and is used daily by individuals and organizations to protect sensitive information.
In the vast and often enigmatic realm of the Darknet, where anonymity and privacy are paramount, locating the right resources can be a daunting task. Unlike the surface web, where mainstream search engines like Google index millions of websites, the Darknet operates on a completely different level. It is home to thousands of hidden websites that end with the “.onion” domain extension, and these sites can only be accessed using the Tor network.

The CSO Guide To Top Security Conferences
Most other clearnet domains for similar services either just redirect, or share their own onion alternative. This is also a reason why I didn’t place it higher up on this list. Out of the 10 sites shown on the first page for each search, there mostly are only 2-3 unique websites. Any search engine mentioned here is not to be taken as an endorsement. Start with verified directories like Ahmia or Hidden Wiki, use a secure environment (VM + VPN + Tor), and stick to ethical, research-oriented content only.
It publishes a newsletter in multiple languages and not only runs onion services for its website but all its email and chat services. Facebook is aware of attempts by many governments to restrict access to a tool that allows strangers across the web to talk and collaborate freely. While its .onion address doesn’t make it much easier to maintain an anonymous account, it does make Facebook more accessible in places where it’s censored.