
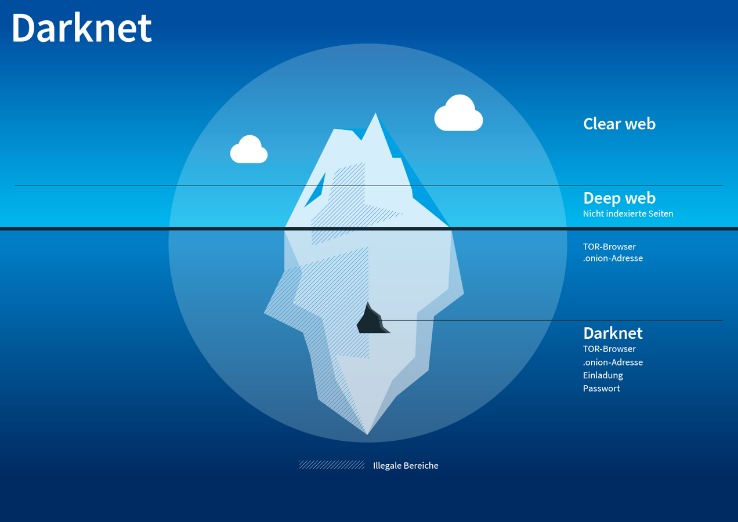
In addition, the content on the pages don’t need any special or custom configuration to access. Yes, you can still be tracked on the dark web despite its privacy features. Tracking can happen through IP leaks, browser vulnerabilities, or malicious exit nodes.
The dark web consists of websites that use encrypted .onion domains, which require specific software and protocols to access. The Darknet is a subset of the Internet operating over encrypted, anonymous overlay networks that require special software like Tor, Freenet, or I2P. Also, set up two-factor authentication (2FA) to add an extra layer of protection in case someone manages to figure out your password.

OSCP Bootcamp In Pune Master Offensive Security With Hands-On Train
- It is the dark web’s version of Wikipedia with a massive links directory.
- The dark web is used by journalists, whistleblowers, and political activists who need the protections that it offers.
- The dark web allows people to access and share all sorts of illegal and explicit material without judgment or censorship.
- LibreY stands out by supporting dark web image search, text results, and torrent links, making it user-friendly and accessible for beginners looking to explore the dark web.
- Tor’s elaborate onion routing technique makes web tracking extremely difficult, but it’s still possible for third parties to spy on certain aspects of your web activity.
Bohemia popped up post-Hydra takedown and brings a fresh vibe—drugs (weed, pills, some coke) and digital goodies like hacked logins, no exact listing count, but it’s growing fast. They take BTC and Monero, and the site’s got a sharp, modern look—vendor profiles are loaded with ratings and reviews, easy to skim. What’s dope is their forums—real talk, not just noise—building trust like Telegram’s side hustle vibe. Escrow’s standard, keeps things fair, and I’ve never seen it glitch out. For 2025, they’re hyping a peer-to-peer escrow twist—could cut out middlemen and shake up how deals flow, which I’m stoked to see play out.
A Brief Overview & History Of Darknets & Dark Markets
Although reported as active, there is limited information on Not Evil’s current status, so availability may vary. More often than not, law enforcement is targeting the sellers more than the buyers. Still, it isn’t unheard of for people to be arrested for buying drugs on DNMs. Just because the seller has good reviews does not mean you can trust them. There’s nothing stopping sellers from packing up and leaving the market at any time.

There are useful resources on the dark web, and you need a dark web search engine to find them. A curated collection of darknet resources for educational purposes, offering insights into darknet frameworks, tools, and security practices. The surface web is publicly indexed, the deep web requires login or credentials, and the dark web is intentionally hidden and accessed via Tor or I2P. Use platforms like Dark.fail or Onion.live to check uptime, domain authenticity, and community trust levels before accessing a dark web site. Yes, platforms like DeHashed, LeakLooker, and DeepPaste provide access to data breaches and leaked credentials. Onion.live is a platform that tracks the status of dark web sites and provides trust ratings to help users verify site legitimacy.
Understanding OAuth 20 And OpenID Connect A Simple Guide For Secure
Chainalysis says that $790 million worth of cryptocurrencies were used to shop in darknet markets during 2019. While some studies have claimed that illegal Bitcoin activity is as high as 44%. There are multiple search engines on the dark web that can help you find what you’re looking for. DuckDuckGo’s no-track dark web search service can be accessed in the Tor browser and is an excellent resource for information about the dark web. Other dark web search engines include Not Evil, Torch, Haystack, and Ahmia.
Dark Web Search Engines: How To Search The Dark Web Safely
Fortunately, in Hidden Wiki, every website is followed by a brief description so that the user knows what to expect. You can also take a look at the blogs & essays section if you want to find some nifty coding resources. Well, now it’s time to fire up Tails and do a little bit of tinkering. Chill, because nobody will ever find a record of you ever fiddling around the darknet.
How To Gain Safe Access To The Dark Web Marketplaces
Just like on the regular internet, phishing is a big problem on the dark web as well. Fraudsters create fake versions of popular darknet sites to trick users into entering login details or personal data. If you fall for it and log in, they immediately steal your credentials and either sell or use them for other scams. As we mentioned earlier, not everything sold on dark web markets is illegal.
Legitimate Use Cases For The Average User
Accessing it requires special software, such as the Tor browser, which provides anonymity by routing your connection through multiple servers. The best way to protect yourself from the dangers of darknet markets is to simply avoid them altogether. Even browsing these sites can put you at risk of malware infections or attract unwanted attention from law enforcement. Installing the Tor Browser is the best way to access the dark web. However, your online activity is encrypted and hidden from view thanks to Tor’s onion routing. This means your ISP can’t see that you’re accessing the dark web (or indeed, the specific sites you’re accessing).
In 2017, a global police operation brought down AlphaBay, the dark web’s largest illegal marketplace, shaking the underground economy. Meanwhile, cybersecurity experts monitor the dark web, scanning for stolen data and emerging threats. If your information surfaces in these murky depths, there’s very little you can do – but knowing the risks involved is a first step toward defence.
When you purchase using links on our website, we may earn an affiliate commission at no extra cost to you. For several years, Yahoo was at the apex as the internet’s best web service provider, offering… It is a relatively new provider but offers better features than most established VPNs. In addition, it has an automatic kill switch (Network Lock) that stops traffic if the VPN connection fails. Accidental leaks at the Tor entry nodes can potentially expose your IP address. The provider also offers a dedicated CyberSec suite that prevents annoying ads and blocks malware and trackers.
Darknet markets trace their origins to the early 2000s, with the advent of Tor in 2002 by the U.S. The first notable marketplace, Silk Road, launched in 2011 by Ross Ulbricht (aka Dread Pirate Roberts), revolutionized online black markets by integrating Tor, Bitcoin, and an escrow system. As a user or cybersecurity professional, approaching these marketplaces demands utmost caution, thorough knowledge of operational security, and constant awareness of legal boundaries. Understanding both the benefits and dangers ensures safer interaction and more informed decision-making in an ever-changing digital environment.
Is It Illegal To Just Browse The Dark Web?
Dark web search engines exist, but even the best are challenged to keep up with the constantly shifting landscape. The experience is reminiscent of searching the web in the late 1990s. Even one of the best search engines, called Grams, returns results that are repetitive and often irrelevant to the query. Link lists like The Hidden Wiki are another option, but even indices also return a frustrating number of timed-out connections and 404 errors. As a result, the dark web has become a breeding ground for illicit activities because government agencies face significant challenges in identifying the operators behind hidden services.
What Is Phobos Search Engine?
You should stay away from everything labeled “porn”, “card skimming services”, “PayPal hacks”, “firearms”, “real fake IDs and passports”. Believe me – there are plenty to go around and each and every one of them are being kept under surveillance. Not to mention the fact that you’ll get exposed to some stuff that will definitely make you take several cold showers. I strongly recommend surfing on the dark web using virtual machine software instead of your locally installed Windows.
Exclusive Monero usage signals a heightened prioritisation of anonymity. This early detection allows organizations to identify and respond to threats quickly, reducing the chances of unauthorized access, financial loss, or damage to brand reputation. Organizations need automated dark web monitoring to prevent cyberattacks.



