
This proactive approach helps investigators stay ahead of potential threats and identify ongoing criminal operations. This structured process ensures security while maintaining the anonymity of both buyers and sellers, making Dark Web marketplaces a persistent challenge for cybersecurity enforcement. Bohemia maintains 22,000+ listings and $3M monthly BTC trades, with a 6% market foothold. The typical cost of credit cards being sold in the darknet markets can range from USD $1 to $25 for each card.
Safeguarding The Netflix Architecture: Unveiling Potential Security Vulnerabilities
Genesis Market extensively used a payment processor called UAPS, so much that the processor’s average inflows fell by 25.7% after Genesis closed last April. Regardless, UAPS remains a key provider of payment infrastructure to top fraud shops. As far as financial recourse for victims, some banks and insurance companies have provided payouts and will include those funds as damages in lawsuits against Genesis Market cybercriminals.
How KELA Cyber Supports You In Darknet Monitoring And Risk Mitigation
ReliaQuest analysts identified that the platform generated over 136,000 customer alerts in 2024 alone, highlighting its significant impact on global cybersecurity. Despite these efforts, dark web operators rebuild quickly, often with better security and decentralized tools. Market takedowns create temporary disruptions, but they rarely dismantle entire networks. Sophisticated players shift operations, adopt new aliases, and resume business within weeks. Litecoin, Zcash, and Dash also see usage, though Monero and Bitcoin dominate the dark web. Some marketplaces have even mandated Monero-only transactions, underscoring a strong preference for privacy-focused coins over traceable ones.
Threats To Personal Data
The website allows a personalized searching experience, where you can search according to your geographical location, country-specific, and keyword or price-specific search results. Below are the best marketplaces on the dark net that we hand-picked after going through multiple shops and doing extensive research. In general, we have noticed an overall increase in the frequency of corporate database advertisements on the dark web. For example, on one popular forum, the corresponding number of posts in August-November 2024 increased by 40% in comparison with the same period last year, and peaked several times. Revenues for the fraud shops on the right side of the chart declined, suggesting their dependence on UAPS for payment infrastructure.
Explore The Products
Ransomware groups increasingly leverage Darknet forums to recruit affiliates, trade exploits, and launder stolen funds. Cryptocurrencies serve as the backbone of these operations, allowing attackers to collect ransoms without tying payments to specific financial institutions. As a result, the overall volume of cryptocurrency tied to ransomware has grown, driving law enforcement agencies to invest in advanced blockchain analytics. These markets sell a range of illegal goods and services, including drugs, weapons, stolen data, and counterfeit items, and they typically require special software like Tor for access. Classic darknet markets sell diverse illegal goods; data stores focus on leaked or stolen data like credentials, databases, and ID records.
Secure Your Cryptocurrency Transactions

It really helped shift the conversation I think away from victim-blaming to this is a gigantic problem. News rooms are facing it and American companies and Western companies all over the world are facing this, and it’s been going on for a really long time. Platforms like SecureDrop enable individuals to submit documents and communicate securely with journalists, thereby exposing corruption and wrongdoings while preserving their anonymity. The significance is in safeguarding the right to free speech and the role of the press as watchdogs.
- The vulnerability could’ve been used to access the market’s database and expose its servers’ IP addresses.
- Alphabay uses AES-256 with PGP, mandatory for its 25,000+ users, while optional 2FA is adopted by 70%.
- Its Tor routing holds a 94% uptime, with rare pauses tied to seller onboarding spikes, not attacks, showing solid tech.
- This section delves into the crypto trading landscape of onion marketplaces, exploring adoption trends, wallet strategies, and conversion tools for navigating crypto trading platforms in 2025.
- It has a huge and active user base as well as a marketplace that makes trading of hacked credentials and stolen data seamless.
Increase In High-profile Law Enforcement Operations Against Cybercrime Groups
By using encryption tools and cryptocurrencies like Bitcoin, cybercriminals can mask their identities and transactions, making it difficult for law enforcement agencies to track them down. Figure 8 is an example of a sample of an Australian passport template which has the same passport ID details but has different photos of individuals. The seller of the below template also shares that any details in the passport including the photograph can be changed and it would still look legitimate. The seller provides full editable versions of the template in .psd format which is an Adobe Photoshop document format.
Software vulnerabilities and “exploits” are used to get remote access to both stored information and information generated in real time. Credit Score reports are one of the most highly traded PII (personally identifiable information) in the darknet markets. A credit score report is an analysis report of the credit worthiness of an individual and the credit score depends on the credit files of a person. Financial organizations use credit score reports to assess a client’s credit history which is used to approve loans. Credit reports are not only used by financial organizations but many others like governments, insurance, and many other organizations which require a credit history to process a request. The price of the credit score lists depends on the score of the report, with the higher score reports going for a higher price.
Use our “Check Status” tool or forums like Dread—our top 10 average 92%+ uptime. Look for ratings below 90% or no escrow history—scams cost $500K+ in 2024 on Torrez alone. Check longevity (1+ year), response times (under 24 hours), and reviews (e.g., Alphabay’s 100,000+), avoiding new vendors with fewer than 50 trades. XMR’s 40% adoption across top 10 (e.g., Incognito at 45%) reflects a 15% rise from 2024, driven by BTC tracking exposing 10% of trades.
- It has a bidding feature, with new batches of stolen data being frequently added.
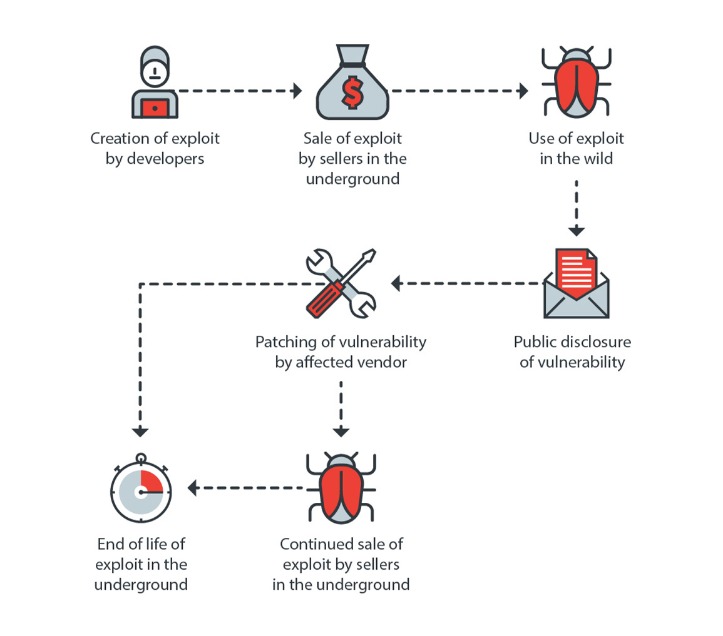
- They’re the tools that enable cybercriminals to conduct their attacks on businesses, institutions, and individuals.
- “Over the years some markets … developed a robust catalog of illicit services like money laundering, fiat offramping, and products that enable cyber-criminal activities like ransomware and malware attacks.
- These enforcement strategies have proven effective in disrupting illicit operations, but new marketplaces continue to emerge, requiring continuous cybersecurity assessment and monitoring.
- Businesses have plenty of opportunities to fortify their defenses against the lurking threats of the dark web.
So, that was my first front row seat to the lengths that nation states would go to try to get access to journalist sources. See how our intelligent, autonomous cybersecurity platform harnesses the power of data and AI to protect your organization now and into the future. Also, the forums tend to be recruitment grounds for a wide range of cybercriminal groups. It’s a type of collaboration that cybercriminals look for to expand their reach as well as the impact of their operations. Also, the forum served as a promotional as well as recruitment platform, whereby malicious actors and other ransomware groups use it to expand their visibility, bolster reputations, and exchange ideas. Still, while it’s a little easier to access it now, it remains reserved and designed for elite users who value privacy.
The digital currencies provide anonymity, and they’re hard to trace, which makes them the best option for illegal transactions. The forum has undergone several transformations since it appeared several years ago, evolving from a platform that focuses on illicit drugs to a huge forum that’s focused on cybercrime. Its members have a key goal to provide key resources for the Russian hacking methods to ensure that they maximize efficiency. Also, the forum features a straightforward joining process to test the skills and proficiency of its potential members.
Crypto Diversification
I ultimately ended up sitting down with Ivan Arce who is one of the older godfathers of the scene. One thing that Ivan told me was the next generation has these other opportunities. MUSIC They don’t need to just work in the penetration testing business when they can make so much money selling a single zero-day exploit to a government or to a government broker.

Complicating matters further is the widening use of alternative channels, such as Telegram groups, private forums, and even hidden social media communities. While .onion services remain central to Dark Web commerce, these additional platforms give cybercriminals greater flexibility and resilience. They can quickly pivot from one network to another in response to marketplace shutdowns or law enforcement scrutiny, making it increasingly difficult for investigators to pinpoint and dismantle criminal enterprises. You can use dark web monitoring tools, such as NordVPN’s Dark Web Monitor, to check if your data has been leaked.
Malware-as-a-Service (MaaS) – or “subscription” – is a dark web business model that involves leasing software to carry out cyberattacks. Typically, clients of such services are offered a personal account through which they can control the attack, as well as technical support. It lowers the initial threshold of expertise required by would-be cybercriminals. They lure crypto users to scam sites and Telegram bots under various guises, and add crypto-stealing functionality to infostealers and banking Trojans. With the price of Bitcoin setting record after record, the popularity of drainers specifically designed to steal cryptocurrency tokens from victims’ wallets is likely to persist in the coming year.


