Sophisticated players shift operations, adopt new aliases, and resume business within weeks. BidenCash and other exit-scam markets such as Torzon and Kingdom Market collapsed between 2022 and 2024. They used “free data dumps” and emotional marketing to build trust before vanishing—an enduring lesson in the risks of social engineering. Many operators have since moved to accepting only Monero (XMR),” Chainalysis added. Freshtools was established in 2019 and offers various stolen credentials, accounts, and host protocols like RDP.
Exodus Marketplace
First things first, always use strong and different passwords for each account you open. As Telegram has end-to-end encryption and anonymous profiles, it makes it an ideal choice for threat actors and hackers to take advantage of. As mentioned earlier, launching a cyberattack doesn’t require any hacking skills.
Similar Content Being Viewed By Others

Nonetheless, the dark web remains accessible to a wide audience, highlighting the need for continued vigilance in combating illegal activities online. Dark web marketplaces provide a platform for illicit transactions, often favoring cryptocurrencies such as Monero, known for its enhanced privacy and anonymity. These marketplaces have become popular hubs for illegal activities, enabling users to buy and sell illicit goods and services with relative ease. Today’s action against Hydra and Garantex builds upon recent sanctions against virtual currency exchanges SUEX and CHATEX, both of which, like Garantex, operated out of Federation Tower in Moscow, Russia. Wanton disregard for regulations and compliance by persons that run virtual currency exchanges will be rigorously investigated, and where appropriate, perpetrators will be held accountable.
Beyond the digital landscape, I seek solace in the open road, riding my cherished motorcycle and experiencing the exhilarating freedom it brings. These moments of liberation propel me to think differently, fostering innovative perspectives that permeate my work. Merging an unconventional background in Law with over 15 years of experience in the realm of technology, I’m on a quest to design digital products that genuinely make a dent in the universe. Cybersecurity experts should pay close attention to these trends, as they often indicate emerging threats and profit-generating tactics among the cybercriminal forums. Telegram channels supplement traditional onion sites, blurring lines between the dark web sites and more mainstream communication tools. Most transactions are done using Bitcoin, Monero, or Ethereum due to their pseudonymous nature.
- The site’s slick—vendor stats update live, checkout’s a breeze, and the vibe’s modern without being over-the-top.
- Stolen credit card numbers, bank login credentials, and identity documents are consistently in high demand.
- Today’s action also reinforces OFAC’s recent public guidance to further cut off avenues for potential sanctions evasion by Russia, in support of the G7 leaders’ commitment to maintain the effectiveness of economic measures.
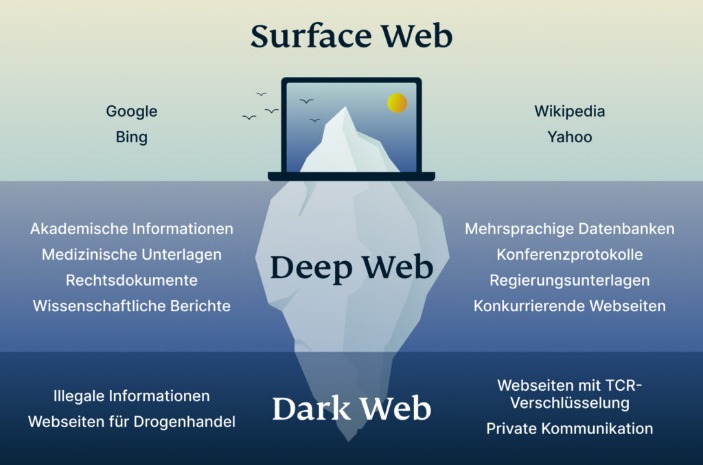
- Many darknet marketplaces uses .onion links that are only visible in the Tor browser.
- The use of privacy-focused cryptocurrencies or mixing services can further enhance the anonymity of transactions, making it more difficult for authorities to trace the source or destination of the funds.
- We find that multisellers have the largest median income throughout the period of observation—except in the last quarter of 2017 and 2018, when they have the second largest median income.
Stolen Financial Data
This extra privacy makes it much harder for authorities to track down who runs these markets and where they are located. For these reasons, most of these stores naturally like the dark web due to its protection. These geopolitical dynamics intensify the complexity of cybercrime, creating multi-layered threats that affect both public and private sectors globally. Decentralized autonomous organizations (DAOs) even govern some of these markets. Such models ensure that the market remains community-controlled and resilient to outside interference. Monero’s ring signatures, stealth addresses, and RingCT obfuscate transaction details—enhancing privacy and hindering traceability The Rise of Monero.
Explicit And Illegal Content

Code exploits target a project’s smart contract code and allow an attacker to remove funds from DeFi protocols without authorization. Code exploits are facilitated by coding mistakes and errors, such as unchecked external calls, access control issues, and logic bugs. Of the USD 1.4 billion stolen via code exploits in 2022, authentication issues, improper validation, and signature verification issues accounted for about 90% of the amount stolen.

How KELA Cyber Supports You In Darknet Monitoring And Risk Mitigation
The platform is favored by cybercriminals seeking access to accounts that can be exploited for fraud or sold to others. The Russian Market has been around since 2019 and is one of the more prominent dark web marketplaces. In this post, we’ll walk you through the top 10 dark web marketplaces that you need to watch for potential threats to your organization. TRM Labs research has also found bridge-hopping to be a favored money laundering methodology used by CSAM actors.
Top-10 Dark-Web Marketplaces In 2025: Overviews, Use-Cases, And Risks
Adapting to the evolving consumer preferences and the fluctuating geopolitical landscape has highlighted the need for agile and responsive Dark Web Intelligence strategies. Besides, the study maps the leading as well as the fastest-growing regional markets. It further enables stakeholders to identify the key country-level markets within each region. And beware—while many explore out of curiosity or for research purposes, it’s important to remember that engaging with these platforms, even as an observer, can lead to serious legal and ethical consequences. Since 2020, 2easy has sold massive stealer logs with sensitive data like passwords, bank cards, and initial access credentials. It supports operations in multiple languages and operates on both clearnet and Tor.
From 2013 until 2015, the multiseller network grows in terms of connectivity, showing an increasing number of edges spread across different markets. During 2016 and 2017, the edges are polarized by AlphaBay, the dominant market (see Fig. 3). Then, between 2017 and 2018, there is a drastic structural change in the multiseller network structure due to operation Bayonet, after which the connections almost vanished. This change persists until the end of the observed period of the data set (also see Supplementary Information S4). These critical changes may not be perceived from macroscopic measures of the ecosystem as a whole. For instance, the typical net income of sellers is seemingly unaffected, as shown in Fig.
Shifts In User Behavior And Marketplace Structures
Addressing these issues requires adaptive legal frameworks, cross-border collaboration, and advanced monitoring tools. Clear compliance standards for crypto firms and financial institutions are crucial to balancing risk mitigation with industry innovation. As digital finance evolves, striking a balance between innovation and security is crucial. Implementing AI-powered fraud detection, enhancing oversight, and promoting responsible adoption will help build a more transparent and resilient crypto ecosystem. Whereas, Pyramid schemes focus on recruitment rather than legitimate products, often disguised as crypto investments.

Related Articles From The Business Security Section
Behrouz Parsarad (Parsarad), residing in Iran, was the sole administrator of Nemesis. In this capacity, Parsarad established Nemesis and held full control over the marketplace and its virtual currency wallets. Parsarad enriched himself from fees he charged users of Nemesis with every transaction, pocketing what OFAC estimates to be millions of dollars over the course of the marketplace’s existence.
STYX Market focuses specifically on financial fraud, making it a go-to destination for cybercriminals engaged in this activity. Accessing darknet requires using Tor Browser, a special web browser that routes your internet traffic through a global network of relays managed by volunteers. This way, it becomes very difficult to trace which websites you’re visiting, and these sites won’t know where you are located. The darknet, also known as the dark web, is a concealed section of the internet that’s inaccessible via standard search engines.
Some high-risk exchanges also operate as parasite exchanges, and usually have lax or non-existent KYC and AML processes. This makes them attractive platforms for cybercriminals who want to launder money or fund illicit activities. Administrators of such exchanges claim to earn 0.5%-1.0% commission on the transaction volume, depending on the share of revenue allocated to advertising and affiliate marketing necessary to drive traffic to their exchange.