No user names are tied to actual identities, and no moderation like one may find on Reddit. Users leverage these platforms to organize protests, whistleblow, share survival guides, or share files P2P. The good news is that the platform will not see what you copy/paste. Your data is encrypted in the Tor browser before reaching the ZeroBin servers.

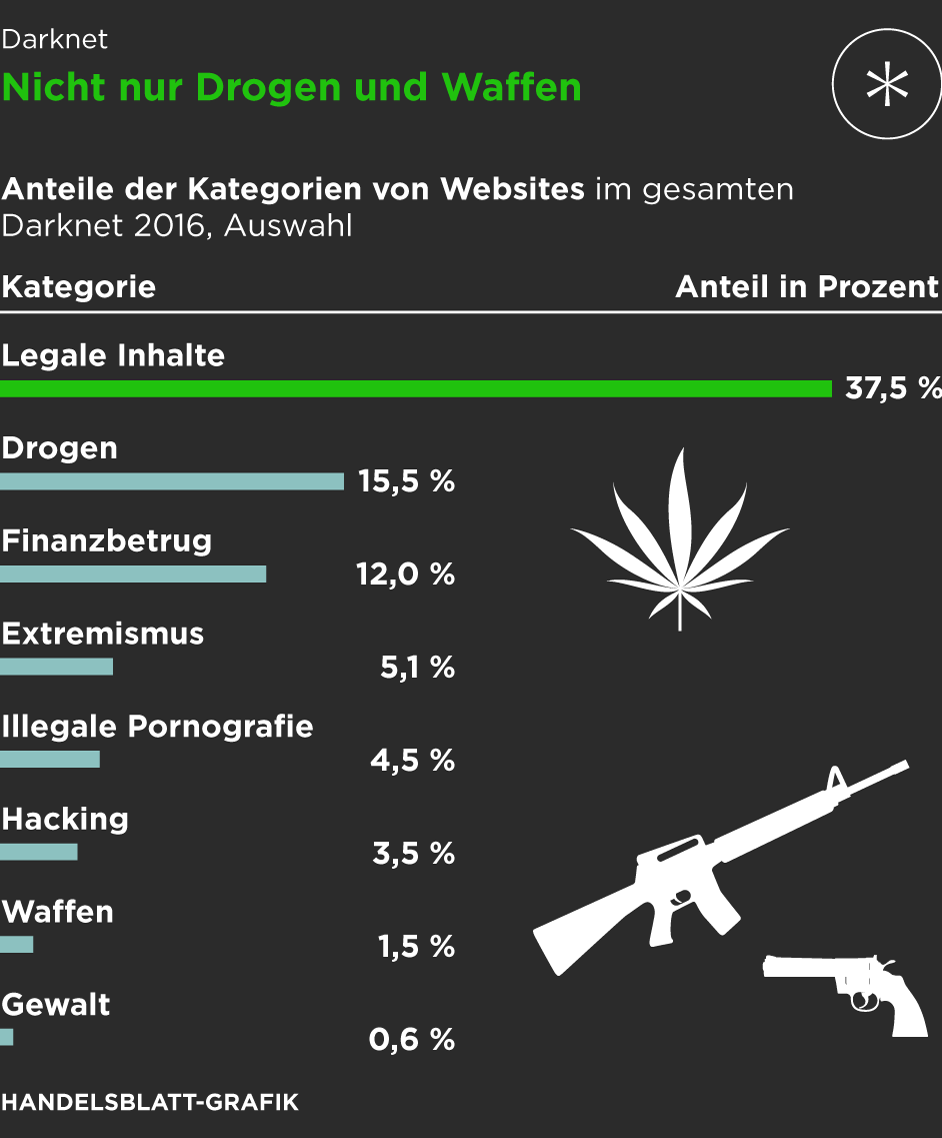
Möglichkeiten Darknet Vs Internet
As a result, you should avoid opening unfiltered sources, torrent sites, and dark web links unnecessarily and downloading every file you come across. With rising online privacy concerns in the current digital age, the Tor network’s anonymity is becoming essential. It is a good way to prevent third parties from tracking online activities. People in countries with heavy internet censorship must get a VPN or Tor browser to access the surface web.
Whether you’re looking to enhance your cybersecurity knowledge or stay informed about dark web activities, our platform is your trusted source. Stay ahead of threats and ensure your online safety with our regularly updated content. Taking the necessary precautions makes tracing your activities on the dark web difficult. For example, I strongly advise using a reliable VPN like NordVPN. Although the Tor browser has sufficient encryption, combining it with a VPN offers better protection.
Brauche Ich Ein VPN, Um Zugriff Auf Das Dark Web Zu Erhalten?
Although the underground internet world is rife with everything bad, it also hosts positive elements. It then depends on you, as the user, how you surf the dark world. However, most are outdated and have not kept up with the changing landscape. For example, DuckDuckGo is the most popular but often shows repetitive results and is sometimes unrelated to the question. A top-of-the-line VPN network that ensures maximum security while accessing dark sites online. The most interesting thing about NordVPN is its built-in Onion over VPN feature.
Struktur Von onion-URLs
Onion sites aren’t really dangerous, but they could be when accessed through unfamiliar or suspicious links. Many reputable websites and news outlets like ProPublica and SecureDrop often share official domain addresses of onion sites on their pages. Some users also share links on encrypted apps like Telegram or Keybase that you can check. RiseUp is a top dark web website that offers secure email services and a chat option.
Setzen Sie Auf Das VPN #1 VPN
It is a component of Whonix, an operating system that functions as a whole inside a virtual computer. It includes all the essential productivity software, including MS Word and an email client. However, there are some significant variances in the background despite the similarities. For example, Whonix’s virtual workstation machine connects to the internal virtual LAN.
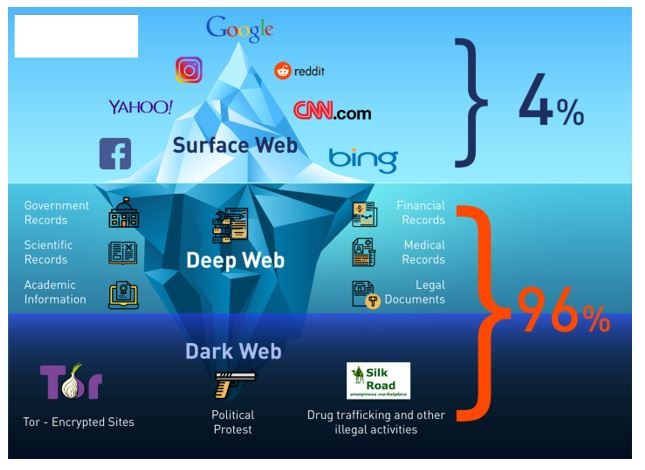
Darknet: Zugang Zur Dunklen Seite Des Internets
Wasabi is one of the most popular cryptocurrency wallets on the dark web. It allows you to search for images, maps, files, videos, social media posts, and more. Sci-Hub is a massive database that eliminates the barriers to getting scientific knowledge.
Was Ist WPA2 (Wi-Fi Protected Access ?

Also, use an effective antivirus program to check threats if you decide to download files. You can check out this guide on the best antivirus software applications today. ActiveX and Java frameworks are susceptible to being exploited by hackers.
It encrypts your traffic at the entry node and changes your IP address. This means you will get a VPN’s security and enjoy the anonymity of the Tor network simultaneously. A virtual private network (VPN) is a good way to mask Tor activities. Today, many organizations exist that are created only to handle these reports anonymously and effectively. They know how to process the information and get it to the correct law enforcement agencies internationally. Since malware lingers across the dark web, your device can easily become infected, even if you are an unsuspecting user.
Ist Es Legal, Das Darknet Zu Nutzen?
Instead, they are designed using a cryptographic key and can be accessed only through software like the Tor browser. The Dark Web is the part of the deep web that is not indexed by search engines, like Google or Bing. For this reason, you cannot browse through these sites using your default search engine.
Purchases through links on our pages may yield affiliate revenue for us. We review and list tools and products without bias, regardless of potential commissions. This is an estimated reading time to let you know how long it will take you to read all the content on this particular PrivacySavvy.com page. However, it has a sneak peek, easy guide steps, and/or a quick list providing quick in-page navigations and easily-found answers if desired. At Dark Web Insights, we go beyond simply exploring the hidden aspects of the internet.
If you’re lucky enough, you can find it on clearnet privacy forums. His articles have appeared in many respected technology publications. Ruheni explains complicated technical concepts clearly and simply. He advocates digital freedom and online privacy at every level. It hosted over 7,000 .onion categorized links to make surfing the web easier. One of Daniel’s impressive features was the built-in functionality that showed whether a particular dark website is online.
- Overall, Subgraph OS is a secure and privacy-focused operating system well-suited for high-risk environments.
- Most likely, the native account on your device has full admin permissions by default.
- It can only interact with the gateway, the most effective method by which the browser protects user applications from learning a device’s IP address.
- Unfortunately, it requires you to have an invitation code to create an account.
- It is the dark web’s version of Wikipedia with a massive links directory.
Ist Das Dark Web Illegal?
You can also check out this ultimate dark web safety guide to browse safely. If you get a reliable vendor, you should procure the services to stay safe when accessing the dark web. You can also run a dark web scan to see if your information has been leaked on the dark web. This dark web monitoring will help you track illicit activities and minimize the risks of cyber-attacks.