Malicious files might bypass Tor’s security, giving away your real IP address. If you must download files, ensure you’re using a separate, secure environment — such as a virtual machine. Always run the latest version of the Tor Browser to protect against security vulnerabilities. Outdated versions may contain weaknesses that attackers can exploit to compromise your anonymity. I recommend enabling automatic updates and checking for new versions before each session.
PayPal Problems: Users Should Now Consider This Now
With it, they can spy on people, steal their sensitive data, or secretly control their devices. These software are also capable of launching DDoS attacks and phishing campaigns. On the dark web, you don’t need to be a technical expert to design ransomware, and that’s dangerous. Even people with little to no knowledge can buy ready-made ransomware and launch attacks on their victims. Later, in 2013, Silk Road caught the attention of law enforcement and policymakers like US Senator Charles Schumer, who publicly called for a federal crackdown.
Marketplaces
However, unlike commercial search engines, This is run by a confederation of volunteers. The site started as a fork of the ahmia search engine, this will remain a central part of the site. At the moment they are making minor improvements to the search engine and working on the Beta version of their new link directory. On hidden wiki you will find a long list of working Onion V3 links to dark web sites, simply use these links in TOR browser to visit them.
Top Dark Web Links – Sicher & Verifiziert 2025
Tor, the most widely used, anonymizes traffic through layered encryption and random routing, providing a secure way to access dark web directories safely. I2P, though less popular, offers similar peer-to-peer anonymity with a focus on internal network services. Together, these technologies facilitate private, censorship-resistant access to hidden content, with the Hidden Wiki acting as a trusted directory to navigate this complex landscape. Without these tools, neither Google nor any surface web browser can reach these secure, hidden parts of the internet. Before the Hidden Wiki’s creation, the dark web was an intimidating, hard-to-navigate space.
Its strength lies in regular updates and community-driven verification of links. I especially like how TorLinks categorizes links based on their type, letting you easily find what you need. N 2025, dark web websites frequently change domains and are often short-lived.
Bonus: A Few More Dark Web Websites

Want to get illegal drugs, fake passports, Trojan, or other cyber attack software? It brings in vendor reviews from other places and verifies them using PGP signatures, so buyers can feel a bit more confident about who they’re dealing with. There’s also a premium account option for users who want extra benefits.
It often hosts copyrighted materials without permission, violating many countries’ copyright laws. Downloading or distributing such material is against the law and can have legal consequences. This means that using the dark web may attract attention from your ISP or even law enforcement. To reinforce your privacy while on the dark web, consider adding on a VPN like Windscribe as an extra layer of protection.

Illegal Pornography
Watch for unexpected changes in system performance that could indicate malware. Cryptocurrency miners and other malicious software often target dark web users. Using a reliable antivirus to scan your device is worthwhile if you spot suspicious spikes in system resource usage. SecureDrop stands out as the leading platform for secure document sharing used by major news organizations. This open-source whistleblowing system enables anonymous file transfers with strong encryption.
It emphasizes anonymity while providing familiar social media features. Some content can be unmoderated, though, so it’s worthwhile to be careful while using this platform. Alt Address provides disposable email addresses specifically designed for dark web use. This service helps protect your primary email when signing up for .onion services. I found it especially useful for testing new services without risking my main email address, though messages expire after 24 hours. DigDeeper offers in-depth analysis of technology and privacy topics rarely covered by mainstream media.

Use HTTPS Whenever Possible
- The dark web comes with its own set of tools and services, including web browsers and search engines (which I’ll get on to in a moment).
- Founded around 1999 by activists in Seattle, it has since grown to over six million users worldwide.
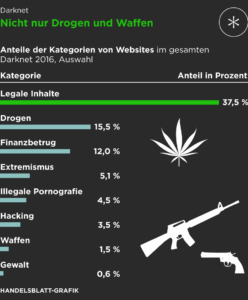
- This includes darknet markets selling drugs, weapons, counterfeit documents, hacking services, and other illicit goods.
- One of its best features is Anonymous View, which is a free proxy that masks your identity while you’re browsing sites.
Even though DuckDuckGo is the Tor browser’s default search engine, it doesn’t index dark web websites, which means you won’t be able to find .onion sites with it. To do that, you’ll need a dark web search engine like Torch or Ahmia. SecureDrop is an anonymous file-sharing platform designed for secure communication between whistleblowers and journalists. While anyone can use it, it’s built for high-stakes exchanges, making it overkill for routine file sharing or data backups.

How Can I Safely Access Onion Sites?

The dark web is a small part of the much larger “deep web,” which also isn’t indexed by search engines — but authorized users can access it using common web browsers. The deep web is made up of email platforms, workplace portals, subscription services, and banking websites — basically anything that requires a login. The “surface web,” on the other hand, is the publicly available part of the internet that search engines index. DuckDuckGo is a search engine available on the Tor network that lets you browse the surface and dark web. Essentially, it’s a search engine like Google or Safari, but unlike other search engines, it doesn’t track your browsing activity or collect user data. So, search results won’t be based on your browsing history, location, or anything else.
HIDDEN WIKI
Disable JavaScript in Tor until you trust the site you’re visiting. Go to the security settings and set the security level to “Safest” to minimize potential vulnerabilities. This encrypts your communications with websites, providing an additional layer of security. You can use the HTTPS Everywhere extension, which comes pre-installed with Tor Browser, to automatically enforce secure connections whenever they are available. To understand the dark web is to embark upon a journey through its historical milestones. To help you make educated choices about cybersecurity to keep you (and your data) safe and secure, by providing detailed, accurate, and practical information based on thorough testing.
As we mentioned earlier, not everything sold on dark web markets is illegal. As terrible as its reputation may be, some vendors sell legitimate goods or services. Some customers even use the dark web to make anonymous purchases, especially in areas where privacy is a huge concern. The marketplace supports multiple payment methods, including Bitcoin (BTC), Litecoin (LTC), and Cryptocheck. They add new batches of stolen data every other week, and there’s even a bidding system where buyers can place offers on new data batches as soon as they become available.