
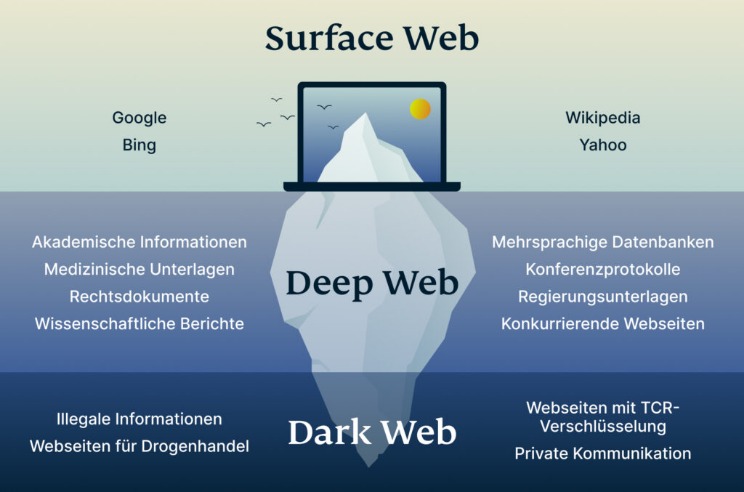
Darknet marketplaces like to exist on the dark web because it offers a service that the regular internet, or more accurately, the “surface web,” does not. Onion sites (aka Tor sites) are websites only accessible on the dark web; you can’t view them using a regular browser. Their URLs (aka dark web links) have .onion as the domain, instead of the common surface web domains like .com or .net.
These markets often facilitate the sale of illegal drugs, weapons, stolen data, and other contraband. Supporting these activities can have serious societal implications and contribute to organized crime and other harmful practices. It is also important to note that not all dark web markets are trustworthy. There have been instances of market exits scams, where the operators shut down the website and disappear with the users’ funds. This highlights the need for due diligence when choosing a deep web market URL or darknet mirror to ensure reliability.
Key Cyber Threats Facing The Financial Sector In 2025
If you connect to your VPN and fire up Tor Browser, you’re using Tor over VPN. All your device’s internet traffic first goes to the VPN server, then bounces through the Tor Network before ending up at its final destination. Your ISP only sees the encrypted VPN traffic and won’t know you’re on Tor.
- Any site that ends with .onion can only be accessed through TOR.
- Users’ identities are safe from the prying eyes of governments and corporations.
- Since malware lingers across the dark web, your device can easily become infected, even if you are an unsuspecting user.
- Our solutions empower you to monitor illicit darknet marketplaces and track emerging threats, ensuring you can take proactive measures to protect your organization and reputation.
- Features such as two-factor authentication, end-to-end encryption, and regular security audits ensure that user data and transactions remain secure.
Best Free VPNs For The Dark Web In 2025: Secure & Fast

Active for a decade since 2014, it is a widely used credit card shop used to source stolen credit card information such as dumps, CVVs, Wholesale Accounts. It maintains a very strict level of user verification and integration with an official Telegram account to provide real-time updates to users. Various cryptocurrencies such as Bitcoin and Monero can be used to make purchases. Security researchers have been monitoring forums within the cybercriminal underworld to investigate the leading markets operating in 2024. One of the most common is the exit scam, where a marketplace suddenly disappears and takes everyone’s money with it. There’s also a privacy angle—some users live in countries with censorship or surveillance, and the dark web gives them a space to communicate or access information more freely.
These search engines neither track your search queries nor record any information, improving digital privacy and keeping your data private. Using a dark web search engine is a great step towards enjoying a more secure experience while shopping on the platform. Not all marketplaces you want to visit can be accessed through regular search engines. In addition, mainstream search engines also track your searches and collect personal information. Cypher marketplace has been on the list of the best dark web shops for a while and deals with the business of a variety of products and services.

Other Privacy Tools And Services
Darknet markets are known for their anonymous nature, providing users with the ability to buy and sell illegal items without revealing their identity. The use of cryptocurrencies, such as Bitcoin, is common in these markets to facilitate the discreet transactions. Once you’ve set up Tor and have the necessary browser settings in place, you can start exploring the dark web.
Abacus Market
I2P uses one-way tunnels, so an eavesdropper can only capture outbound or inbound traffic, not both. Journalists and whistleblowers, including Edward Snowden himself, often use the dark web and Tor to exchange sensitive information. For instance, the Ashley Madison data dump was posted to a site only accessible to Tor users. So, if you want to know how to access the dark web safely, you need to understand that the vast majority of the dark web, or dark net, is only accessible through the Tor browser. It’s like an iceberg – The visible tip above water, known as the “surface web” represents the familiar, searchable content.
Is Claude Safe And Secure In 2025?
You can’t just Google “Silk Road” and hope to land on the dark website. Officially, the Tor Browser is only available on Windows, Mac, Android, and Linux. Many experts advise against using third-party mobile browsers that utilize the Tor Network. No standard web browsers can be used to access dark web content.
Ares Market Features

It is used by many for buying or selling items that are prohibited on the regular internet, like fake IDs, illegal drugs, and stolen data. Naturally, this makes the dark web a breeding ground for illegal activity. But onion sites can also serve nobler goals, like providing access to information and independent journalism in countries with government censorship. A VPN protects your connection against everyone, not just your ISP and the authorities. This process also prevents your ISP from seeing your data or where it’s going.
One of the standout features of top darknet markets is their escrow system. This mechanism holds funds in a secure account until the buyer confirms receipt of the product, reducing the risk of fraud. Additionally, multi-signature transactions are increasingly common, requiring multiple parties to approve a payment, further enhancing trust between users. These features collectively create an environment where the drug trade can thrive securely and efficiently, meeting the demands of a growing user base.
The dark web is a breeding ground for hackers, and dark web markets offer various hacking tools and services for sale. These might include exploit kits, hacking tutorials, DDoS-for-hire services, stolen data, and other hacking-related resources. The Onion Routing Protocol (TOR) is an essential tool for accessing the deep web market and ensuring anonymity while browsing through various dark web links. TOR works by encrypting and routing internet traffic through a network of volunteer-operated servers, called nodes or relays, which are located all around the world. Some dark markets require registration, while others allow anonymous browsing and purchasing. These platforms often use rating systems to establish trust and reputation within the community.
Activists, whistle blowers, and journalists also use the dark web to communicate securely with sources and news organizations. You can also use Brave to access the dark web on your computer.
This growth is supported by the increasing sophistication of security measures, ensuring that users can engage in transactions with confidence. The combination of advanced technology and community-driven accountability makes these platforms a reliable choice for secure trading. The diversity of offerings on darknet markets has expanded significantly, catering to a wide range of user preferences.



