
Accidental leaks at the Tor entry nodes can potentially expose your IP address. Many services that are allegedly offered on the dark web are scams. Some services are genuine; you can get what you want at an agreed fee.
Acronis Cyber Protect Cloud: New Version C2505
The site’s dead simple to use, and vendors leave feedback that’s actually helpful. I’ve noticed they’re big on local vibes—vendors tweak their stock for where you’re at. With 2FA and escrow, it feels safe enough, and it rarely goes offline. Crypto services use various measures to keep cryptocurrency wallets secure and make sure your Bitcoin is safe. Some, such as Wasabi Wallet, provide an extra layer of security by using onion routing to pass crypto activity through multiple nodes, none of which know the sending and receiving IP addresses. In addition, Darknetlive has a list of dark web vendors, which is very convenient — it offers detailed information about each vendor, including .onion addresses (in alphabetical order) and FAQs.
What Are Autoshop Marketplaces
Malicious vendors often infect buyers with spyware, ransomware, or infostealer malware hidden in downloadable files. Some listings are nothing more than scams designed to trick people into sending cryptocurrency without delivering anything in return. Dark web markets work much like regular e-commerce websites but with extra layers of anonymity and encryption. Buyers browse listings, place orders, and pay with cryptocurrency — typically Bitcoin or Monero — to obscure transaction trails. Social media platforms like Facebook and news sites like the BBC and ProPublica have also waded into the dark web’s waters.
- ZeroBin encrypts and decrypts text in the browser, so their servers have no way of knowing what’s happening on the browser side.
- It’s divided into commercial links (from crypto services to gambling sites) and non-commercial links (like social media).
- With its nifty “conjoin” feature, users can combine different coins in one transaction, covering the user’s tracks and maintaining their anonymity.
- Also, since users can only access them using the Tor browser (with its high-end encryption), users can be rest assured their identities and locations remain hidden.
Table Of Contents
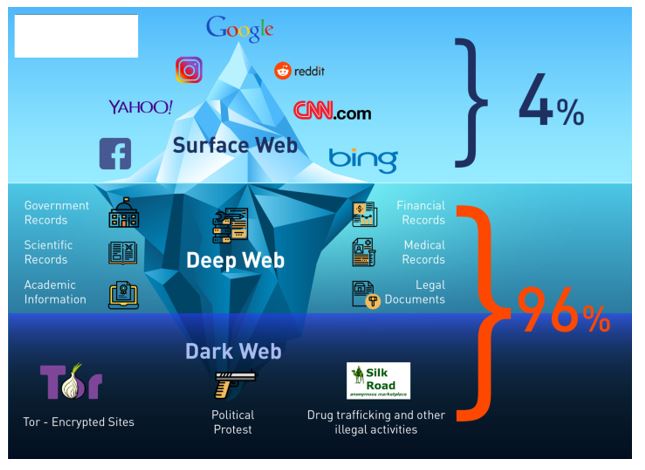
A network browser gives you access to sites with the ‘.onion’ registry operator. Lastly, the dark web is the portion of the deep web that is generally inaccessible and is much larger than the surface web. It relies on P2P connections and requires specialized tools and software. Tor and I2P are the two commonly used tools for accessing the dark web to provide anonymity.
The Top 10 Darknet Marketplaces Of 2025
One thing that distinguishes BidenCash on the dark web, however, is how it markets itself. These markets are dangerous anyway and shouldn’t be accessed even if they’ve onion addresses. It has a search option to let you find local and international products and services on the dark web. A lot of vendors from all over the world are registered here, offering an extensive range of products, including digital services, security tools, and other equipment.
A Quick Guide On How To Use A VPN With Tor
However, it’s very difficult and would require extensive resources, meaning that the average person’s identity is unlikely to be uncovered. For example, ProPublica—a renowned investigative journalism non-profit— uses the dark web to communicate with whistleblowers and ensure readers can access content without facing retaliation. That is important for those who may fear persecution for their actions or live in areas where access to information is regulated.
Hidden Answers
This is an estimated reading time to let you know how long it will take you to read all the content on this particular PrivacyRadar.com page. However, it has a sneak peek, easy guide steps, and/or a quick list providing quick in-page navigations and easily-found answers if desired. Activists, whistle blowers, and journalists also use the dark web to communicate securely with sources and news organizations. These domain names are not registered with a central authority but are instead derived from cryptographic keys. Offering books for free, shadow libraries face the morality question of copyright vs. access to information and knowledge.

These “onion” sites are only accessible on the dark web and bear the “.onion” domain at the end of the URL. This is no different from the “.net” or “.com” of the regular Internet. So, whether you seek refuge from oppressive regimes, are searching for answers to hard or embarrassing questions, or are trying to share confidential information securely, there is something for you.
How KELA Cyber Supports You In Darknet Monitoring And Risk Mitigation
We ensured that the dark web sites we chose had reviews and feedback from real users on other forums; this way, we can be sure of the site’s reliability and legitimacy. It is a good website for finding out which websites are currently working. If you need a listing of currently active websites, contact their support, and they will provide you with that.

This makes it more difficult for authorities to locate and take down these sites. The clearnet is the regular internet you’re used to using, where network traffic origins are fairly easy to pinpoint. While this topic may seem distant for most people, understanding how these spaces operate is crucial. It helps us stay more vigilant, better protect ourselves, and make informed decisions online.
This particular marketplace surfaced in the middle of 2017 and had remained active ever since. However, it’s worth noting the website does not contain multisim like other marketplaces do and don’t force vendor PGP, but there is 2FA to help you stay protected while buying online. Even after Silk Road went down, dark web marketplaces haven’t slowed down. Stopping their growth takes serious effort from US agencies like the FBI, often working hand-in-hand with international law enforcement. The buyers, or “consumers,” are cybercriminals who use these tools to launch illegal activities. The victims, who are common users, businesses, and even banks, who end up paying the price.
‘It’s Happening Everywhere’: 1 In 3 ICE Detainees Held In Overcrowded Facilities, Data Show
Monero’s ring signatures, stealth addresses, and RingCT obfuscate transaction details—enhancing privacy and hindering traceability The Rise of Monero. Sites such as Abacus and Russian Market accept both currencies to broaden their appeal. Exclusive Monero usage signals a heightened prioritisation of anonymity. Exodus Marketplace emerged in early 2024 as a successor to Genesis Market, focusing on malware-harvested device logs. It reportedly controls around 7,000 infected endpoints across 190 countries Top 10 Dark Web Markets.



