Additionally, raising awareness around responsible gun ownership and promoting alternatives to violence can contribute to a safer society. By fostering open discussions and providing accessible resources, we can encourage individuals to seek peaceful means of conflict resolution instead of resorting to firearms. Typically sold in bulk lots of a hundred or more, credit card numbers can be had at low prices and ready for the most illicit of uses.
They know how to process the information and get it to the correct law enforcement agencies internationally. Immediately close your entire Tor Browser window (not just that active tab). Note that engaging with the content in any way is not only distressing but could also put you at legal risk. While Tor offers anonymity on the dark web, your online activities leave breadcrumbs that can reveal your identity.
Most darknet services offer worldwide shipping with some exceptions to Russia due to their strict import controls. One of the Armory’s most easily recognizable items is a $2,800 AK-47 rifle that is on sale, down from the sticker price of $3,600. The markdown is still many times over the legal price for this firearm. An American law called the National Firearms Act says this gun must be entered into a government registry upon purchase.
- “We don’t have enough courts, we don’t have enough judges, and we don’t have enough police officers to tackle the real scale of illegal behaviour on the internet.
- Investigating crimes related to the dark web typically requires specialized training and technological expertise.
- There are several email and IM services which you can use, and it’s highly recommended to pick one if you want to step up your dark web game.
- Additionally, raising awareness around responsible gun ownership and promoting alternatives to violence can contribute to a safer society.
- A study from the RAND Corporation analyzed the size of the firearms trade on global cryptomarkets, finding that the darknet has indeed increased the availability of firearms for similar prices to the illegal street trade.
How Are Guns Sold On The Dark Web?
It is a relatively new provider but offers better features than most established VPNs. In addition, it has an automatic kill switch (Network Lock) that stops traffic if the VPN connection fails. Accidental leaks at the Tor entry nodes can potentially expose your IP address. The provider also offers a dedicated CyberSec suite that prevents annoying ads and blocks malware and trackers.
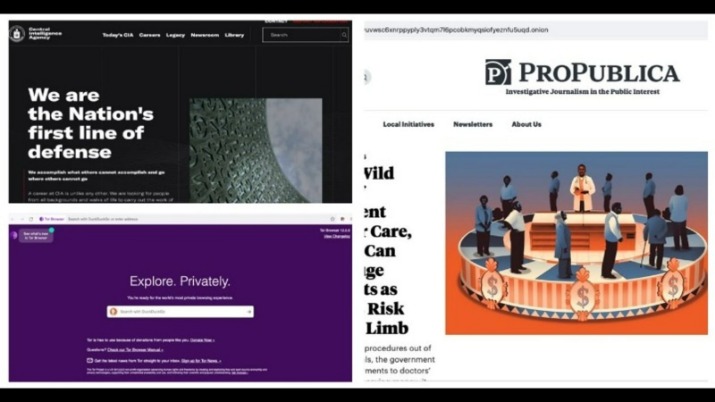
This network of over 6,000 relays hides your location, thus protecting you from online surveillance and third-party tracking by your websites. Established in 2012, the platform is a time capsule that collects snapshots of websites. These onion addresses will remain online even if the original page disappears. It also keeps the graphical copy and text of the page for better accuracy. The BBC news website has a special .onion site, which you need to access via the dark web.
Risks Involved In Purchasing Guns On Dark Web
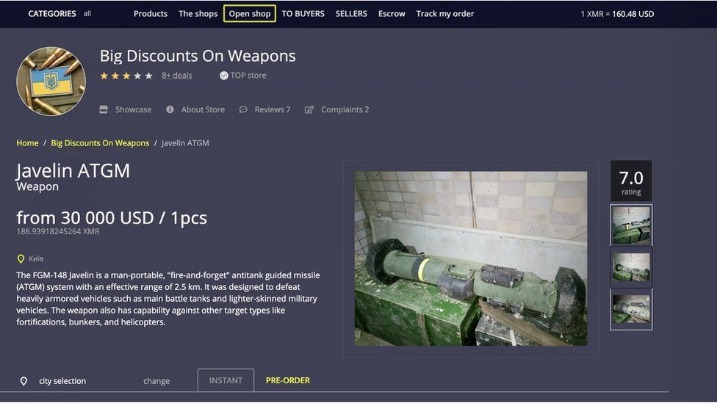
Another vendor on “Thief” is “Big Discounts on Weapons,” which offers a U.S.-supplied Javelin ATGM anti-tank missile system for $30,000. KELA has stated that many of these listings are spread on pro-Russian Telegram channels and Russian media outlets, usually shortly after publication on the sites. The most prevalent ‘ship to’ destination, from the same vendor over many cryptomarkets.
Secret Purchases
The latter almost doubled after the terrorist attacks in Paris and Brussels. In Germany, the amount of legally registered weapons has increased by almost 10 percent in five years, and there were 6.1 million guns in 2017. Between 2012 and 2017, the number of permits to carry weapons for use outside shooting clubs more than tripled to 9,285. The dark web began as a channel for anonymous communication, making it attractive to hackers and criminals. While there is a long history of connections between drugs and weapons, DarkOwl analysts were curious if a similar relationship could be observed between weapons and human trafficking, and drugs and human trafficking.
DOGE Gets The Green Light To Slash Gun Regulations At ATF
Another notable security trick Wasabi uses to verify transactions is the Neutrino protocol. It assigns a task to the client instead of the server, eliminating server-related vulnerability. It has a feature called CoinJoin that combines multiple coins from different users into a single transaction. This makes it extremely difficult to find out who you are transacting with.
The last section will examine rarer items and urban legends (hitmen and Red Rooms). The report found conventional handguns were most popular on the dark web with illicit market vendors offering stealth packaging to Australia. Such interactions can occur within private groups or forums dedicated to specific interests, including weapon collection or tactical training. This interaction enhances the informal network of people engaged in this illegal trade, promoting a culture of secrecy and trust among individuals with shared interests. The rise of the dark web as a weapons marketplace presents several unique challenges for law enforcement agencies worldwide.
Types Of Weapons Available
It is crucial, however, that law enforcement agencies keep pace with evolving technologies and methodologies employed by dark web vendors to maintain efficacy in combating these illicit markets. Another significant factor in the dark web’s role as a weapons marketplace is its global reach. Traditional weapons trafficking often faces geographical limitations, hampered by border control and customs checks. Conversely, the dark web permits sellers from one country to reach buyers in another without crossing international borders physically. This capacity to transcend geographical boundaries complicates law enforcement efforts, as legislation and enforcement vary by country.

Combating The Trade: Strategies And Solutions
This is a great way to improve your privacy because Tor isolates each website you visit, meaning third-party trackers and ISPs can’t reveal your identity. One option is to try DuckDuckGo’s .onion version, which is great for privacy. Other options include Ahmia and NotEvil, which focus on listing .onion links. Cryptocurrencies such as Bitcoin have been the dark web currency even before they became available to the general public.
Data Leak Checker: Has Your Email Been Hacked?
People mostly use it for covert communication, anonymous tips submission, and stuff like that. In terms of functionality, I don’t think there are too many differences between regular IMAP, POP3, and SMT services and the stuff you can use to communicate on the dark web. Although content on the dark web is not as ‘indexed’ compared to the one on the clear web, you can still use search engines to find stuff. Chill, because nobody will ever find a record of you ever fiddling around the darknet.
‘Very In-Your-Face And Real’: Kurt Cobain Described Recording Technique That Gave ‘In Utero’ Its Classic Sound
- However, it also featured a weapons section where firearms were exchanged.
- I2P, or the Invisible Internet Project, allows you to access the ordinary and dark web.
- Business had been booming lately what with all the riots both sides want to be armed, my usual base of gangs, mafia, and various criminals, and not to mention the whole quarantine.
- Agents made seven attempts without giving any information to suggest that they were prohibited from owning a gun.
- This deep web gun site lists many weapons and ammunition; you can buy handguns, Ammo, and rifles, as mentioned on the site.
They also mention their stealth practices to avoid detection, including that pistols are taken apart and hidden in power tools. For example, FREEGUN advertises that they work directly with smugglers and offers worldwide shipping with the exceptions of North Korea, Sudan, Tunisia, Algeria, Egypt, Iran, Iraq, Syria, and Paraguay. Yes, Statista allows the easy integration of many infographics on other websites. Simply copy the HTML code that is shown for the relevant statistic in order to integrate it. Our standard is 660 pixels, but you can customize how the statistic is displayed to suit your site by setting the width and the display size. Please note that the code must be integrated into the HTML code (not only the text) for WordPress pages and other CMS sites.
If the above average Joe’s explanation isn’t enough for you, below are some legitimate reasons to use the Dark Web in a bit more detail. Tor anonymity comes with a cost since malicious hackers and criminals like to operate in the shadows. For example, perpetrators of trafficking and cyber attacks use the dark web to disguise their actions. Remember that illegal activities can still incriminate you, whether you are using a Tor browser.