Hiddenwiki.pw is not liable for any loss or damage incurred as a result of using the above links. If the VPN connection fails, the automatic kill switch will kick in, temporarily breaking your traffic. Since Tor has to pass your traffic through several nodes, it will slightly slow your speeds. You can use the Smart Location feature for the fastest connections.

Tor and I2P are the two commonly used tools for accessing the dark web to provide anonymity. The anonymity provided by onion routing comes at the cost of slowing your internet considerably. As such, we do not recommend using Tor if you want to do data-intensive activities like streaming in HD, gaming, torrenting, or making video calls. One option is to try DuckDuckGo’s .onion version, which is great for privacy. Other options include Ahmia and NotEvil, which focus on listing .onion links. In some countries, such as China and North Korea, the government uses heavy online censorship and blocks many dark web websites.
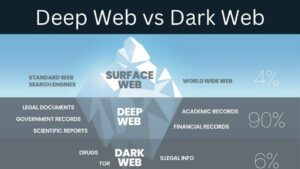
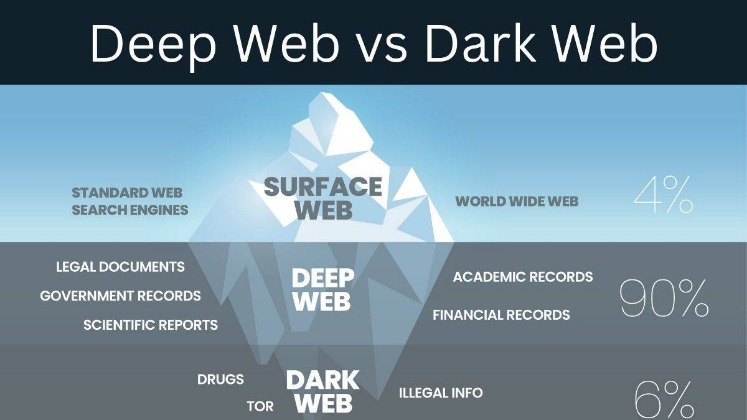
What Kind Of Content Is On The Dark Web?
Its straightforward design allows you to search hidden services without distractions. Candle is particularly popular among users who value speed and ease of use. It delivers quick search results, making it ideal for those who need to find information fast. Additionally, the deep web is increasingly being used for e-commerce.
Navigating The Risks
In this part, we’ll talk about the kinds of information you might find on the Deep Web. It’s actually an open-source search server that you can use to create your own deep web search engine. This might sound not very easy, but it’s easier than you might think. For example, if you’re doing medical research, you could set up Fess to search only trusted medical databases. This focused approach can save you much time compared to broader deep web searches. Crypto services use various measures to keep cryptocurrency wallets secure and make sure your Bitcoin is safe.
It prioritizes user privacy by not storing your search queries or personal data, ensuring anonymity during your searches. LibreY’s clean interface simplifies the process of searching hidden services, making it accessible even to beginners. Today, deep web search engines are evolving to meet the demands of a growing user base. Many search engines now incorporate features like encrypted connections and advanced filtering options. Additionally, hidden wiki websites function as directories of categorized .onion links, providing common entry points for users delving into the hidden internet.
- If this sounds similar to The Wayback Machine, the concept is indeed the same.
- Blockchain.com’s impact on the cryptocurrency community extends beyond its products and services.
- The deep link meaning is all about enhancing user experience by enabling seamless navigation to precise sections of an app, making it an invaluable tool for both businesses and users.
- If you pair the regular DuckDuckGo engine with the Onion version, you can perform an entire web search.
- Tor (The Onion Router) is the program that most people use to get to the Deep Web.
- The dark web is just a part of the internet where users can communicate and browse privately, often beyond the reach of standard government monitoring.
Hosting / Software Services

However, since the dark web is also used for criminal activities, it is not advisable to visit and surf this part of the internet. One can also find drugs, crime services, stolen cards, and other illicit activities being offered by hackers. In contrast, a deep link is a specialized link used in mobile applications and websites to guide users to a particular, often searchable or indexed, piece of content within an app or website. Deep links enable a more focused and targeted user experience, allowing users to bypass app homepages or navigate directly to specific content, enhancing user engagement and usability.
Dicas Importantes: Proteja Sua Segurança Nos Sites onion
While it might appear tempting to venture into the dark web, it’s crucial to understand that the risks here are far more severe compared to the deep web. Therefore, if you do decide to explore it, exercise extreme caution. These sites aren’t just important resources; they’re like lifelines used to serve readers living under oppressive regimes.
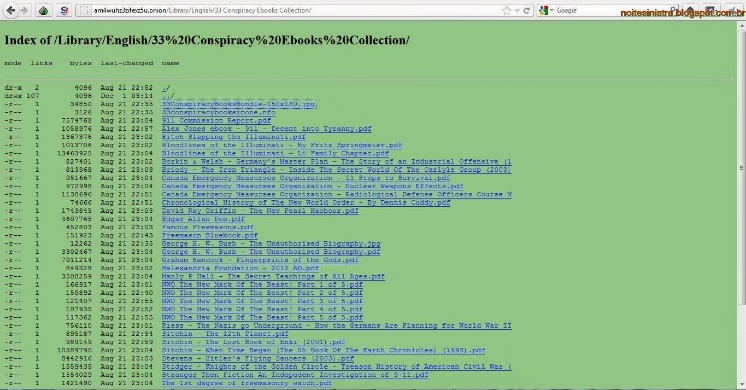
Some sites might use these details for advertising, analytics, or tracking your online preferences. While they might sound the same, these websites are fundamentally different. The Tor browser option for streaming comes with eleven channels with varying genres. But, honestly, if you are going on the dark just to enjoy free music, we recommend that you go for free torrent platforms on the surface web instead. The Imperial Library currently holds around 1.5 million books, some of which may be hosted illegally, and thus, their consumption might violate copyright laws.
Is It Illegal To Surf The Deep Web?
Riseup is an invite-only email and communications service that doesn’t hold onto any of the data you generate when you use it. It describes itself as a tool for social change and “a project to create democratic alternatives.” Riseup requires you to have the onion link as well as an invitation. The dark web is home to a variety of useful and legitimate resources — educational materials, encrypted email services, anonymous forums — that can’t be found elsewhere.
More Security Articles
Sci-Hub, often referred to as a “pirate” academic database, is a groundbreaking online repository that provides free access to millions of research papers and academic articles. As a result, the dark web has become a breeding ground for illicit activities because government agencies face significant challenges in identifying the operators behind hidden services. The dark web consists of websites that use encrypted .onion domains, which require specific software and protocols to access. As a result, Torch is often considered one of the leading dark web search engines.
- Onion sites are dark web sites that can only be reached through online routing via Tor, in which encrypted data passes through multiple nodes before reaching its destination.
- Borderless news reporting and uncensored media are among the most important and practical uses for the dark web.
- The dark web has a lot of good uses, but it is also where many illegal things happen.
- No info is available on the explored institutions or how these sections can be accessed.
- As a non-profit endeavor, not Evil distinguishes itself by adhering to strict guidelines, eschewing illegal services and materials, including adult content, narcotics, and firearms markets.
- It’s a popular choice for users worried about online surveillance and data collection.
As news outlets rarely concern themselves with explaining exactly what it is besides being a place where you can anonymously acquire illegal goods. Cloudwards.net may earn a small commission from some purchases made through our site. Make Tech Easier provides tech tutorials, reviews, tips and tricks to help you navigate the complicated world of technology. If you start to wade into Dark Web waters, it’s not as much about safety as it is about legalities. If you stay in Deep Web territory, there is plenty you can do where online safety isn’t a significant concern. Understanding how to use Tor is one of the best ways to familiarize yourself with the Deep Web and what you can really do.
Popular search terms on Kilos include narcotics, firearms, and fraud-related items, reflecting its role in catering to diverse user needs. You should consider using data breach monitoring tools to regularly check if your personal information has been leaked onto the dark web. Also, be wary of RATs (Remote Administration Tools) that malicious actors might try to install through dark web sites to gain control of your system. Ensuring a secure connection is crucial when browsing the deep web — though Tor encrypts traffic natively, many dark web sites lack SSL certificates. Instead of relying solely on HTTPS, you can verify site authenticity through multiple trusted sources, such as official PGP signatures or well-known directories.
Specifically, the I2P darknet is accessible, while the Tor network is accessible through the Orchid Outproxy Tor plugin. In due course, the framework was remodeled and made public as a secure browser. Some whistleblowers and journalists use these portals to safely leak information, especially when a source requires complete privacy. It has a feature called CoinJoin that combines multiple coins from different users into a single transaction. This makes it extremely difficult to find out who you are transacting with. Also, you can set a strong password to protect your message and choose how long it will take to expire.
This adds extra protection since opening Tor itself encrypts your traffic. We recommend you only visit safe dark web links to explore such as The CIA, Facebook, DuckDuckGo, and Torch. The system is designed to provide enhanced security and privacy features. Its key features include kernel hardening, application firewall, package security, filesystem encryption, meta-proxy encryption, and binary integrity. Another essential security feature is that all incoming and outgoing data from the app is encrypted, including any private and public keys involved.
SimplyTranslate is an onion based language translation service using the google translate engine. It’s an easy and simple way to de-couple your internet usage from Google’s monopoly over the web. One of the most straightforward ways to access to dark web safely is via Tor, so we’ve kept that in mind when compiling our list. Impreza Hosting is a service that helps you host a site on the Tor network.