Transactions within these marketplaces typically leverage cryptocurrencies—most commonly Monero, Bitcoin, and privacy-centric digital currencies developed specifically to enhance transaction anonymity. Monero, in particular, has become the preferred cryptocurrency on the dark web in 2025 due to its advanced privacy mechanisms, which obscure transaction histories and wallet balances from public view. OSINT professionals must venture where conventional tools can’t reach—and the dark web is one such frontier. Certain dark web sellers are also offering potent forms of ransomware in a bundle deal.
Google Play Gift Card Carding Method (Updated Hacks)

Massive bundles of this professional-grade software are being traded for the price of a beer ($5.64), despite notionally being worth thousands of dollars. This new edition of the Darknet Market Price Index investigates the illicit sale of hacking tools on the dark web. We found that it’s possible to dip your toe into online fraud for less than the price of a coffee. Saheed Aremu passionately advocates for digital privacy and cybersecurity in the modern digital age. As one of PrivacySavvy’s resident VPN experts, he guides readers on protecting their online information and anonymity. Saheed earned his degree in Technology and Ethics from the University of Lagos in Nigeria.
The effectiveness of DDoS attacks is achieved by using a large number of compromised computers. Ransomware tends to be more expensive than different vulnerabilities offered for sale. However, their popularity among threat actors and cybercriminals makes them accessible and very easy to find on the dark web. The fusion of AI and cybercrime has elevated the threat landscape beyond traditional security assumptions. Whether it’s a hyper-personalised phishing email or a deepfake voice call from your CEO, the line between real and fake is rapidly dissolving. The RAMP forum is also considered “friendly” to Exploit and XSS, with one key differentiating factor.
IntelX Darknet Search
However, the rise of password cracking tools has made it easier for hackers to break into systems and networks. These tools are designed to exploit weaknesses in password encryption algorithms, making it possible for even novice hackers to gain access to sensitive information. Password cracking tools are readily available on the dark web, and their use is becoming more widespread, as they are becoming increasingly sophisticated. The Shadow Market is a dangerous place where hackers and cybercriminals can buy and sell tools and services for malicious purposes.
Topics And Products Sold
Yes, the darknet still exists and continues to operate through networks like Tor, I2P, and Freenet. While law enforcement regularly shuts down illegal marketplaces, the underlying infrastructure remains functional. New darknet sites and markets continuously emerge to replace those that get shut down. The technology behind the darknet is actively maintained and continues to evolve.
By gaining the trust of other participants, these agents can observe transaction patterns, identify high-level operators, and collect detailed evidence on supply chains. TorZon Market debuted in September 2022 and quickly gained traction with over 11,600 listings, including narcotics, malware, and hacking utilities. Its transparent feedback system, which uses PGP-verified reviews, promotes vendor accountability. With an approximate market value of USD 15 million and support for both Bitcoin (BTC) and Monero (XMR), TorZon strikes a balance between accessibility and privacy-enhancing features. Below you’ll find a table showing some of the major darknet markets Krixo has detected, their URLs, and their current status. Background research tasks included learning from past drug lords, researching legal matters, studying law enforcement agency tactics and obtaining legal representation.

Unlike the Deep Web, Darknets are intentionally hidden and designed to preserve privacy and anonymity. Even platforms like Netflix, which require paid access, are technically part of the Deep Web. There are estimated to be 1.1 billion websites on the Surface Web as of 2025 (Internet Live Stats). The MITRE ATT&CK framework provides a comprehensive view of adversary tactics. Protecting endpoints with Singularity™ Endpoint Security ensures that these threats are detected and neutralized. Watch our cyber team share their key insights from their investigations into the biggest dark web trends in 2022.
Dark Web Scams: How Criminals Trick Buyers And Sellers
Spoofing and phishing tools are highly effective because they exploit human vulnerabilities, such as curiosity or fear, rather than technical weaknesses in the victim’s system. The use of social engineering tactics, combined with sophisticated software, makes these tools particularly dangerous. As a result, they are widely used in a range of cyberattacks, from simple phishing scams to highly targeted attacks against government agencies or large corporations.
The results will either be used for identity theft or sold on the dark web for a profit. It reveals the extent to which streaming and VPN account details dominate the illicit trade in personal data on the darknet markets. They deliberately obscure themselves from the public and can only be accessed through the Tor browser, ideally using a VPN (Virtual Private Network) for additional security. The markets are often used to buy and sell personal data, along with other contraband including weapons and illicit drugs. This marketplace specializes in a variety of illegal products, including drugs, counterfeit documents, and hacking tools.
Notes From The Dark Web: Analyzing Ukraine-Related Chatter In Key Forums
It is a significant threat to businesses and individuals alike, and must be taken seriously. By understanding the nature of the Shadow Market and taking steps to protect against its threats, organizations can better protect themselves against cyber intrusions. The Shadow Market is a marketplace where hackers, cybercriminals, and other malicious actors can buy and sell services.
S Best SOCKS5 Proxies For Secure Carding And Anonymity
But as operations scaled, IRC’s static architecture and lack of mobile adoption left it vulnerable. The torch passed to dedicated darknet forums, often on the Tor network, which allowed marketplaces and vendor reputation systems to emerge. Its mobile-first design, ease of channel creation, and semi-anonymous architecture made it an attractive choice for actors who needed speed and reach more than secrecy. Dark web markets have exploded in scale and reach in 2025, becoming the most dangerous hubs for trading drugs, stolen data, and hacking tools. These anonymous marketplaces—operating mainly on the Tor network—are now a primary threat vector for businesses and cybersecurity professionals.
- Some Crypters and Binders are available for free on the internet, while others are sold on the Shadow Market for a price.
- During its time online, staff members of Knight, Qilin, qBit and other ransomware gangs advertised their affiliate programs, looking for new partners.
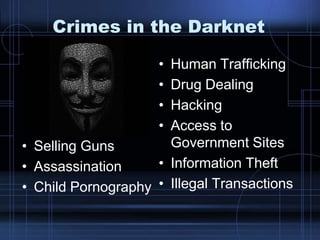
- The markets often share materials related to child exploitation, pornography, and non-consensual recordings, all of which are serious crimes that inflict lasting harm on real-life victims.
- Numerous password cracking software tools are only a Google search away even on the normal web.
Threats To Personal Data
Some marketplace operators first build trust by running a legitimate platform. Understandably, as in the case with most illicit trade markets, you don’t even need to verify your email Awazon. The dark web is designed in such a manner that it hides the identities and locations of its visitors. This extra privacy makes it much harder for authorities to track down who runs these markets and where they are located. For these reasons, most of these stores naturally like the dark web due to its protection. Some Crypters and Binders use a technique called polymorphism, which changes the encryption code of the tool every time it is used.
The growing sophistication of cyberattacks makes it imperative for organizations to conduct regular security gap analysis and implement cybersecurity best practices to prevent breaches. Today, darknets are populated by a vast array of users, ranging from privacy-conscious individuals to cybercriminals, hacktivists, and nation-state actors. These hidden networks provide a platform for illegal activities that include the sale of stolen data, hacking tools, weapons, counterfeit currency, and narcotics. The dark web serves as a hidden marketplace where cybercriminals trade stolen data, malicious software, and hacking tools beyond the reach of traditional law enforcement.
A data breach can also occur accidentally, for example if someone’s login credentials are accidentally published. Others, particularly those based in Russia, focus solely on info stealer hacking tools and brokering stolen data. From drug sales and breached data to scam services and malware, dark web markets are some of the most dangerous corners of the internet. These markets mimic traditional e-commerce websites, but instead of second-hand books or vintage jackets, they traffic in illegal goods and criminal services. When the FBI and Europol announced the takedown of Genesis Market in 2023, a site known for selling digital fingerprints, many expected demand to dissipate; instead, buyers and sellers regrouped on Telegram.
Darknet Markets Explained: Navigating The Hidden Web
Although these marketplaces are continuously shut down by law enforcement agencies, they still work today. Interestingly, new sites get more hype, and it even becomes difficult to shut them down, as they have better security than the older ones. Crypters and Binders are also used in malware attacks, where hackers use malicious software to gain access to a victim’s computer or network. By encrypting malware, hackers can avoid detection by antivirus software and increase the chances of a successful attack. The best way to protect yourself from keyloggers and stealers is to be vigilant about your online security. Use strong, unique passwords for each of your accounts, enable two-factor authentication whenever possible, and be cautious about clicking on links or downloading attachments from unknown sources.