
Activists, journalists, and whistleblowers use the dark web to communicate safely without fear of retribution. The term “dark” doesn’t necessarily mean illegal; it simply indicates a layer of the internet not indexed by conventional search engines. Unlike traditional payment methods cryptocurrencies don’t require personal details like credit card numbers or bank accounts making the transactions more private.
From dark pool markets to escrow networks, this guide maps the underground economy. If you’re lucky enough, you can find it on clearnet privacy forums. If you must explore sites like The Hidden Wiki, do so with extreme skepticism, never download files, never enter personal info, and never send cryptocurrency to unknown sites.

The Ethical Debate: Darknet Marketplaces’ Moral Ambiguity
User reviews and vendor ratings play a critical role in maintaining trust within these markets. Platforms like Empire Market 3.0 have implemented advanced feedback systems, allowing users to evaluate vendors based on product quality, delivery speed, and communication. This transparency fosters a reliable trading environment, encouraging repeat transactions and long-term relationships between buyers and sellers.

Malware Sales
For all these reasons, at PrivacyRadar, we strongly discourage using Awazon or any other dark web marketplaces. It’s for the good that these sites are not available for the general internet user. OnionLinks is a library of dark web links, most importantly, active links.
However, technological advancements such as encryption and privacy-focused browsers like Tor enabled the general public to access it. Some whistleblowers and journalists use these portals to safely leak information, especially when a source requires complete privacy. No one is hiding here—they’re just guaranteeing that people in censored countries can read the news without being flagged. As listed above in our article, even respected organizations like the BBC and ProPublica have a version of their site on the dark web. Keybase is a fantastic onion website that lets you cryptographically bring your different online identities together. Another notable security trick Wasabi uses to verify transactions is the Neutrino protocol.
How To Find New, Active Dark Web Links
Ahmia is a safe alternative search engine for users who prefer the dark web. It also provides insights, helpful statistics, and updates regarding the Tor network. It is important to note that the people or journalists who use ProPublica to spread their truth recognize the risk of doing so. As a result, we want you to stay safe and anonymous by using a paid VPN service whenever you surf this dark web platform.
The Evolution Of Darknet Markets In 2025
However, any illegal activities conducted on the dark web, such as purchasing illicit goods or engaging in criminal behavior, are still punishable by law. Venturing into the darknet without precautions is like walking a tightrope without a safety net. Forest VPN stands out by providing robust encryption and privacy. Cannabis only marketplace with XMR payments, escrow, wallet-less system and modern UI/UX. XMR Only, walletless and accountless market with XMR Multi Sig and escrow service.
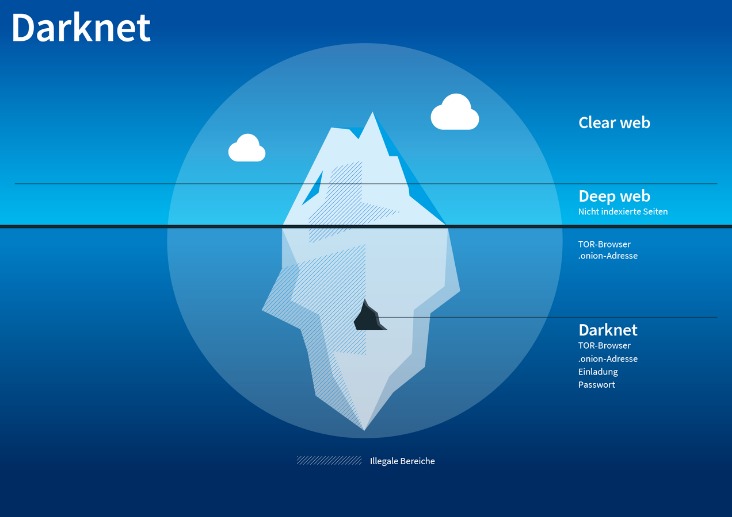
For example, it maintains your privacy and enables you to access untraceable content and services. Some markets even sell privacy tools, but you are more likely to run across counterfeit prescription pills and stolen identities. The Dark Web is the part of the deep web that is not indexed by search engines, like Google or Bing. For this reason, you cannot browse through these sites using your default search engine. Keep in mind that you’ve to use very specific keywords when searching. And most importantly, be patient as you’ve to sort through a lot of useless results.
Hidden Answers
- The darknet in 2025 is a thriving, evolving ecosystem of anonymous marketplaces accessible via Tor.
- Dark web websites are not indexed by standard search engines and can only be accessed using specialized tools, such as the Tor web browser.
- (b) is the deep web, which consists of sites that require a login to access like email accounts, banking portals, and subscription services.
- Onion sites are considered part of the deep web because search engines like Google and Bing can’t index them.
- Read about the adventures of modern-day explorers who have made it their mission to venture into the tunnel network of huge American universities.
- Its look, design, options, and interface are exactly the exact copy of its competitor, but everything else, including buyers, vendors, and servers, is different.
Never trust search engines or third-party lists for darknet market URLs. Using TAILS is yet another security measure that protects your online identity on the dark web. It is a specific Debian-based version of Linux software that leaves no traces of the user activity or the operating system on the computer.
Tor Websites: 10 Links That Offer A Safer Browsing Experience

The anonymity that onion routing provides slows down your internet considerably. For this reason, anybody who wants to privately stream in HD, play games, torrent, make video calls—or do anything else that requires fast speeds—is advised to use a VPN instead. Onion sites do not use regular domain names that are registered with a central authority (domain name registry). Instead, onion sites are derived from a cryptographic key and must be accessed using the Tor browser. It’s not just about access—it’s about responsible access, and that’s what makes OnionLinks the dark web’s most trusted directory.

Tor mirrors for top markets, forums, and vendors are listed, giving you peace of mind. Our goal has always been simple—track reliable, official mirrors of popular dark web markets, and update users when something changes. It is a private search engine that lets you search the regular internet via Tor. This allows you not only to visit sites with the added privacy provided by the Tor network, but also search the web as privately as possible from inside the Tor browser. The mgm grand market distinguishes itself through state-of-the-art security features including mandatory PGP encryption protocols. The mgmgrand market infrastructure incorporates advanced escrow mechanisms paired with thorough vendor evaluation systems.
Plus, it’s slower since your data travels through the same four steps – entry node, relay node, exit node, and then the VPN server. As we mentioned above, when you connect to Tor your data first goes through an entry node, which can see your IP address. By connecting to a VPN before using Tor, you mask your real IP address before it reaches this entry node, adding an extra layer of security and anonymity. Your activities on the dark web are not entirely shielded from tracking, and relying solely on anonymity can lead to a false sense of security.
Run Antivirus/Anti-Malware Software

You could be monitored closely even if you are not doing anything illegal. Remember that illegal activities can still incriminate you, whether you are using a Tor browser. For example, you shouldn’t pirate copyrighted material, engage in terrorism, or share illegal pornography.
It’s also important to note that your activities on the dark web aren’t completely immune to web tracking, and the expectation of anonymity can create a false sense of security. You can run a dark web scan to see if any of your data has leaked onto the black market. And if you think you’ve fallen victim to identity theft or fraud, be sure to report the internet scam just like you would any other crime. The BBC and other well-known news services are blocked in some parts of the world.
An easy way to find content on the dark web is to receive a link from someone who already knows about it. There are often copious amounts of how-to articles, software exploits, and hacked credentials for sale. Not every visitor is a criminal, but this is where most cybercrimes begin.



