
They know how to process the information and get it to the correct law enforcement agencies internationally. Since malware lingers across the dark web, your device can easily become infected, even if you are an unsuspecting user. In some countries, evading government restrictions to seek new political ideologies is punishable. For example, China uses the Great Firewall to block access to Western sites.
Criminal Hacking Services
You can also check out this ultimate dark web safety guide to browse safely. Nemesis was established in 2021 and operated as a criminal marketplace on the darknet, an encrypted network within the Internet that can only be accessed with special anonymity-enhancing browsers. Drug traffickers active on Nemesis sold fentanyl around the world, both on its own and surreptitiously laced into other drugs. On one hand, it offers privacy for whistleblowers, journalists, and citizens in oppressive countries. On the other hand, it’s notorious for enabling illegal activity, including drug sales, weapons trafficking, counterfeit ID trading, hacking services, and the exchange of stolen personal data.
Why Is It Critical To Monitor Dark Web Marketplaces?

You can also run a dark web scan to see if your information has been leaked on the dark web. This dark web monitoring will help you track illicit activities and minimize the risks of cyber-attacks. The dark web also helps individuals communicate about or sell illegal items such as weapons, drugs, malware, etc.
How Can I Differentiate Legitimate Services From Scams On The Dark Web?
Exclusive Monero usage signals a heightened prioritisation of anonymity. Exodus Marketplace emerged in early 2024 as a successor to Genesis Market, focusing on malware-harvested device logs. It reportedly controls around 7,000 infected endpoints across 190 countries Top 10 Dark Web Markets. We’re back with another video in our Webz Insider video series on everything web data. They use pseudonymous wallets, privacy coins (like Monero), mixers, chain-hopping, and non-KYC platforms to obscure transaction trails.
Common Illegal Items
- Due to being the most popular and the oldest coin, Bitcoin is traceable.
- BidenCash was launched in 2022, and since it became a hot spot for cybercriminals to sell and buy illegal things, including stolen card information and personal data.
- Like ransomware, criminals can buy software and inject your devices with viruses.
- BidenCash and other exit-scam markets such as Torzon and Kingdom Market collapsed between 2022 and 2024.
Chill, because nobody will ever find a record of you ever fiddling around the darknet. Note that Tails’ installation package is the .img format, which means that you’ll need software capable of burning images on your thumb drive. Tor relays are servers run by volunteers, designed to keep your activities private and untraceable. Unlike regular browsers that directly connect to websites via your ISP’s DNS, Tor anonymizes your journey by routing your request through several relays before reaching its destination.
Bonus: The Silk Road
Even people with little to no knowledge can buy ready-made ransomware and launch attacks on their victims. Later, in 2013, Silk Road caught the attention of law enforcement and policymakers like US Senator Charles Schumer, who publicly called for a federal crackdown. That push led to the arrest of Ross Ulbricht, the founder of Silk Road, after a long and intense investigation. While you could find all sorts of products on Silk Road, drug sales quickly became prevalent because of the profits it raked in. In fact, by 2013, a Guardian article revealed that about 70% of listings were drug-related.
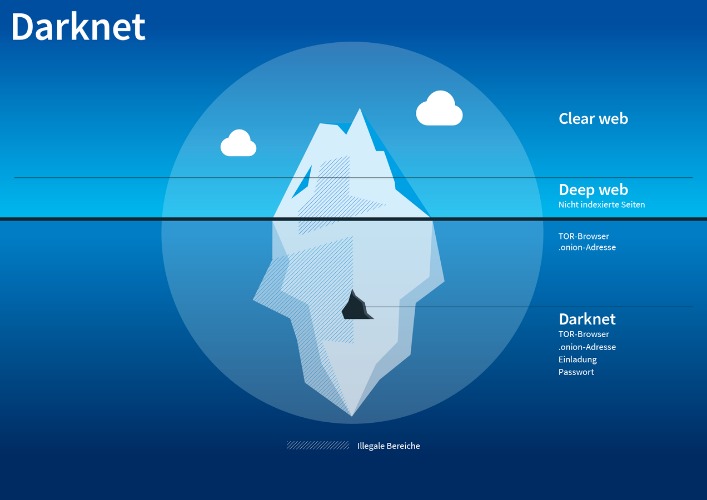
How To Access The Dark Web

So, it’s only natural to find ways to keep in touch with your darknet buddies and/or customers. There are several email and IM services which you can use, and it’s highly recommended to pick one if you want to step up your dark web game. Services like Random Chat connects you with random people using the same service. Although content on the dark web is not as ‘indexed’ compared to the one on the clear web, you can still use search engines to find stuff. If the signal goes through the Tor network first, your ISP will be able to see that you are attempting to connect to a Tor node. Though no one should bat an eye just because you’re attempting to access the dark web, keep in mind that in some countries, like the United States, even a simple foray can get you in trouble.
By 2025, several new and legacy marketplaces have gained dominance. These platforms cater to specialized criminal sectors, making them more efficient and organized. Marketplaces like Abacus Market, STYX Market, and others have evolved into well-structured hubs with user-friendly interfaces, customer review systems, and dispute resolution mechanisms. Their design mirrors legitimate e-commerce platforms, but their operations revolve around illegal products and services. The data collection and analysis steps are presented on the flowchart in Figure 1 and explained below.
- It sells stolen card data — dumps, CVVs, even wholesale batches — and lets users bid on fresh leaks.
- These geopolitical dynamics intensify the complexity of cybercrime, creating multi-layered threats that affect both public and private sectors globally.
- In 2025, alliances between cybercriminal syndicates and state-backed hackers have grown more common.
- It works by sending internet traffic through volunteer-operated nodes all over the world.
- For example, AlphaBay Market – once the largest dark web marketplace – was seized by US and international law enforcement in 2017.
This is a great way to improve your privacy because Tor isolates each website you visit, meaning third-party trackers and ISPs can’t reveal your identity. The social media giant is also aware of the many attempts by repressive regimes to restrict its access. After all, it enables users to connect and communicate with each other from around the world. The patterns revealed in this analysis are not static; they can shift over time due to changes in drug supply, law enforcement efforts, and societal attitudes.

Pixel Privacy believes in digital privacy and does not believe in using it for heinous and/or illegal activities, and so the focus of this article will be on legal activities. The content of all these pages is stored on Google’s servers, but it’s mostly outdated, old content; smartphone app content; journals; court records; private social media profiles, and much more. Ethically, they must minimize harm, responsibly handle any stolen or sensitive data (often notifying victims or law enforcement), avoid entrapment, and maintain research integrity. Discover how to explore darknet market links safely while ensuring your privacy and security. BidenCash and other exit-scam markets such as Torzon and Kingdom Market collapsed between 2022 and 2024. They used “free data dumps” and emotional marketing to build trust before vanishing—an enduring lesson in the risks of social engineering.
So, if the website looks fishy, close the tab, and forget about it. Sure, it’s not as secure as the clear web version, but it’s there and totally legal to use. Hidden Facebook is hardly the only social media client on the dark web.
A logless VPN, which doesn’t store any traffic logs nor session logs is highly preferable. Traffic logs are a bigger concern than session logs, but neither are good. Personal and financial data are commonly sold on dark markets, facilitating identity theft and fraudulent activities. The significance here lies in the potential damage to individuals and businesses. Companies must implement strong data security measures, employ encryption, and monitor for data breaches to protect customer and employee information. Dark markets often employ end-to-end encryption for communication between buyers and sellers, enhancing security and privacy.



