U.S. customers predominantly purchase drugs from these groups that are known to have used crypto to source fentanyl precursor chemicals from labs based in China. The cartels then use those chemicals to manufacture fentanyl that is later sold in the U.S. U.S.-based drug vendors on Abacus Market advertising a synthetic opioid called China White, which its customers can purchase using Bitcoin or Monero. The chart above shows that ASAP and Mega Darknet markets led the large retail and wholesale segments respectively. Looking closer at ASAP Market inflows, it won some share of revenue across all drug purchase types, receiving 37.1% of social supply, 35.7% of large retail, 16.5% of small retail, and 13.5% of wholesale purchases.
C The Tor Network
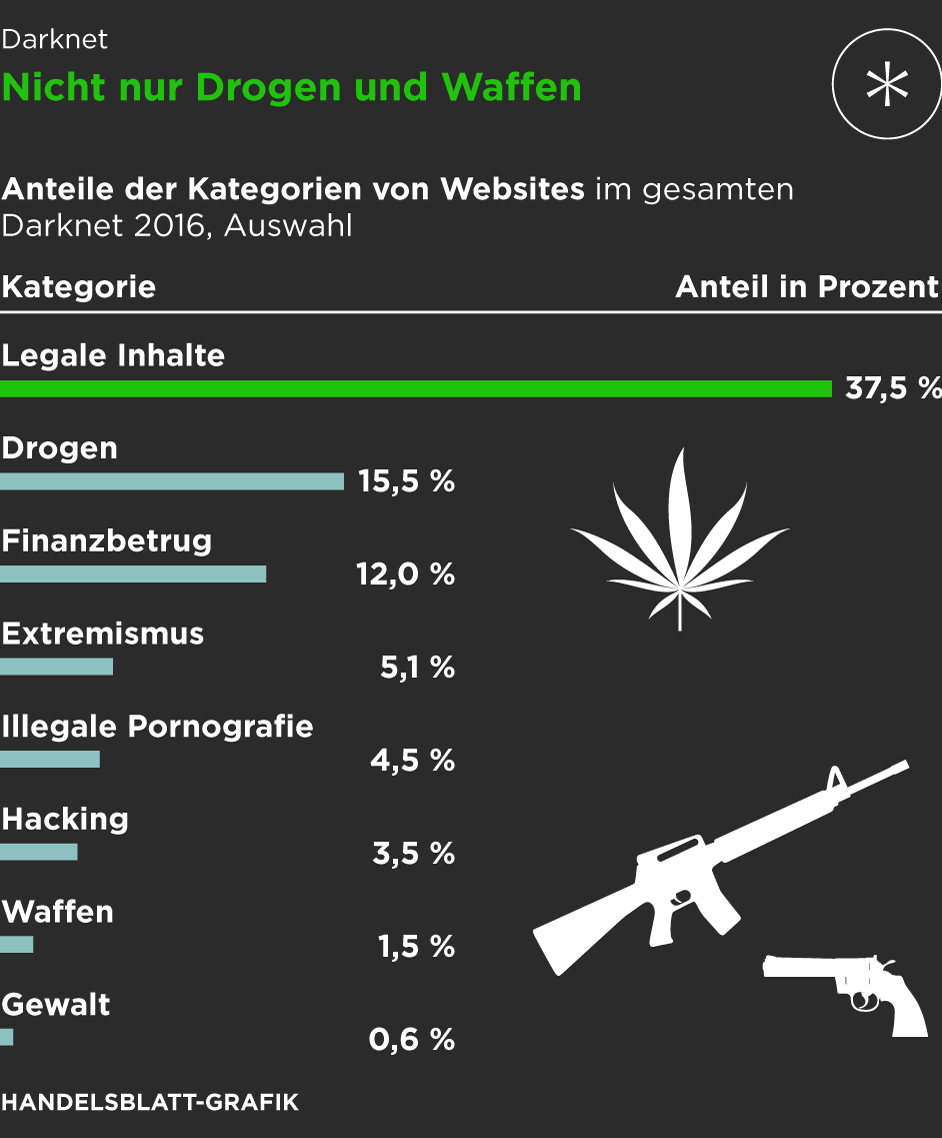
The use of encrypted messaging and secure payment methods ensures that transactions remain private and secure, fostering a thriving environment for trade. Despite Telegram’s anonymity, the dark web is still a hot spot for illegal trading of malware, illicit goods, and stolen data (such as stolen credit card information). Even with the increase in law enforcement pressure, the dark web market still achieved a revenue of $2 billion in 2024. Therefore, as long as this dark part of the internet exists, these marketplaces will flourish and emerge.
Stigma And Inequality: The Hidden Harms Faced By UK Cannabis Patients
Additionally, escrow services are commonly used to safeguard funds until the buyer confirms receipt of the product, further enhancing trust within the community. Unlike traditional search engines, it doesn’t track or store personal information, ensuring your searches stay private. It’s a popular choice for users worried about online surveillance and data collection. Additionally, the integration of Bitcoin and other cryptocurrencies has streamlined transactions, eliminating the need for traditional banking systems.
Explicit And Illegal Content
I also included instructions on how to access the dark web, and outlined how to stay safe when browsing dark web links (the dark web is also home to many scams and malicious sites). The Tor network provides powerful tools for enhancing online privacy and anonymity, but these benefits come with certain trade-offs. Onion websites use onion routing, a technique for encrypting and anonymizing data transmitted over the Tor network. The name “onion” comes from the layered structure of the encryption, similar to the layers of an onion.
ZeroBin — The Secure Way To Share Your Pastes
For this reason, anybody who wants to privately stream in HD, play games, torrent, make video calls—or do anything else that requires fast speeds—is advised to use a VPN instead. Onion sites do not use regular domain names that are registered with a central authority (domain name registry). Instead, onion sites are derived from a cryptographic key and must be accessed using the Tor browser. As a result, your dark web use may draw unwanted scrutiny from your ISP or law enforcement.
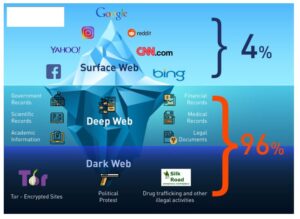
What Is The Dark Web And How To Access It?
This service is a good source of statistics if you have a school project requiring research on Tor and the dark web. However, note that the site only uses non-sensitive and public data for the metrics. The Tor Metrics is a good place to get more information about the Tor project. It collects data from the public Tor network and archives historical data of the Tor ecosystem. Since Hidden Wiki maintains all kinds of websites, ensure you don’t open something you don’t want to see.
This market also features an ‘Other’ section where users can browse delivery services, as well as bank/SIM cards, passports and other identity documents, hacking services, web design, and laboratory equipment/precursor chemicals. As for RuTor’s ownership, this post by user ‘ER1VD4PC’ alleges that new owners of the forum are the Khimprom syndicate, “a large cartel, but alas, already operating under protection,” according to the translation. Such claims couldn’t be fully validated and should be treated with certain grain of salt. Same time, RuTOR may be definitely named one of the longest living underground communities surviving challenging times for other Dark Web actors without significant issues. The community remains online and available for drug sellers 24/7 despite repeated DDoS attacks.

How To Access The Deep Web?
Onion sites aren’t really dangerous, but they could be when accessed through unfamiliar or suspicious links. If you get a reliable vendor, you should procure the services to stay safe when accessing the dark web. You can also run a dark web scan to see if your information has been leaked on the dark web. This dark web monitoring will help you track illicit activities and minimize the risks of cyber-attacks. Your online activity and communications remain private and secret on the dark web. Because of this, some people use it to get around government restrictions, while others use it for illegal activities like smuggling drugs and weapons.
We carefully considered the data structure and conducted spatial analysis to ensure a robust analysis. In our research, we included only the listings containing less than or equal to 5 g of any substance, thereby eliminating outliers and wholesale listings. Listings measured in units or milliliters were also excluded due to the difficulty distinguishing personal purchases from wholesale ones.

- Get the latest in privacy news, tips, tricks, and security guides to level-up your digital security.
- Besides monitoring and improving the network, the data can be used to detect possible censorship or attacks.
- Insights like these help researchers and advocates understand how and why Tor is being used.
- Scroll on to learn more about dark web links (also called Tor links or onion sites), get the right links for some of the best Tor sites, and find out how to visit them safely.
- This paper recognizes that the data it uses originates from the darknet, a virtual illicit market.
Always exercise extreme caution and verify the legality of any services you access. KeyBase combines encrypted messaging with secure file sharing and identity verification. Its dark web version provides the same functionality as the clear web option, while adding Tor’s anonymity layer.

However, legal bodies and law enforcement operations made this impossible and shut down these illegal communities. Genesis Market and BidenCash, two top dark web marketplaces, were also shut down in 2023 and 2025, respectively. As we mentioned earlier, not everything sold on dark web markets is illegal. As terrible as its reputation may be, some vendors sell legitimate goods or services. Some customers even use the dark web to make anonymous purchases, especially in areas where privacy is a huge concern.
Why Are Darknet Markets Found On The Dark Web?
Keybase is a fantastic onion website that lets you cryptographically bring your different online identities together. Another notable security trick Wasabi uses to verify transactions is the Neutrino protocol. It assigns a task to the client instead of the server, eliminating server-related vulnerability. It has a feature called CoinJoin that combines multiple coins from different users into a single transaction. This makes it extremely difficult to find out who you are transacting with. Wasabi is one of the most popular cryptocurrency wallets on the dark web.
Specifically, these manufacturers are becoming increasingly cautious about sharing cryptocurrency addresses in direct communications with buyers. This shift stems from the demonstrated efficacy of blockchain analysis in tracing illicit transactions and aiding investigations. The reduction in the quality and user numbers of Western DNMs stands in contrast to the Russian-language ecosystem, where fierce competition and high profits are driving innovation. 2024 saw 42% fewer new darknet marketplaces (DNMs) launched year over year, with the proportion of Monero-only DNMs launched increasing from little more than a third in 2023 to nearly half in 2024. That is why in 2006 they created “the most private search engine in the world”, which does not record, track, or share your personal data. Over the years, they added many additional privacy features, such as “Anonymous View” for added protection.