Revoke ACCESS privilege to access and run queries against the home database from the specified role. Grant ALL DATABASE PRIVILEGES privilege for all databases to the specified role. Grant TRAVERSE privilege on all graphs and all relationships to the specified role. Grant TRAVERSE privilege on all graphs and all nodes to the specified role. Revoke immutable CREATE ROLE privilege from the specified role. When immutable is specified in conjunction with a REVOKE command, it will act as a filter and only remove the matching immutable privileges.
Quantified path pattern matching a sequence of paths whose length is constrained to a specific range (1 to 3 in this case) between two nodes. Node labels and relationship types can be referenced dynamically in expressions, parameters, and variables.The expression must evaluate to a STRING NOT NULL
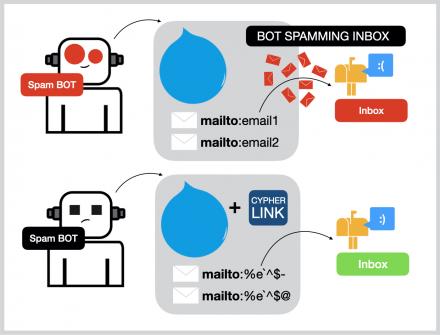
How Do I Use The Secret Code Translator To Encode My Messages?
- The reduce() function returns the value resulting from the application of an expression on each successive element in a list in conjunction with the result of the computation thus far.
- The localdatetime.truncate() function truncates the given temporal value to a LOCAL DATETIME instant using the specified unit.
- As a pioneering and bold venture in the darknet realm, Cypher Market offers an extensive range of products and services, pushing beyond the limits of typical internet marketplaces.
- From AI-powered personalization to seamless cross-platform integration, our aggregator is poised to revolutionize the way you discover, access, and enjoy the finest cypher darknet and cypher darknet market.
- Cypher Market is a new walletless darknet market on the Tor Network that opened in January 2020.
The none() function returns true if the predicate does not hold for any element in the given LIST. The any() function returns true if the predicate holds for at least one element in the given LIST. The rand() function returns a random FLOAT in the range from 0 (inclusive) to 1 (exclusive).The numbers returned follow an approximate uniform distribution. The reduce() function returns the value resulting from the application of an expression on each successive element in a list in conjunction with the result of the computation thus far. The range() function returns a LIST comprising all INTEGER values within a range bounded by a start value and an end value, where the difference step between any two consecutive values is constant; i.e. an arithmetic progression. The keys() function returns a LIST containing the STRING representations for all the property names of a NODE, RELATIONSHIP, or MAP.
List Functions
Also privileges to execute procedures and user defined functions are granted. Grant NAME MANAGEMENT privilege to create new labels, new relationship types, and new property names for all databases to the specified role. The graph.names() function returns a list containing the names of all graphs on the current composite database.It is only supported on composite databases. The localtime.statement() function creates a LOCAL TIME instant. Function returns the current LOCAL TIME instant using the statement clock. Cypher Market has quickly become a notable presence in the darknet marketplace, renowned for its minimalist design that prioritizes a seamless user experience.
Unlock the true potential of your cypher market shopping experience with our innovative aggregator. We’ve revolutionized the way you discover and access the best online marketplaces, empowering you to find the perfect cypher url and cypher mirror with unparalleled ease and efficiency. Our platform’s advanced search tools and personalized recommendations ensure that you’ll always be one step ahead, discovering the latest trends and must-have items before anyone else. Experience the ultimate in convenience, quality, and customer satisfaction as you explore the vast array of cypher url and cypher darknet link our aggregator has to offer.

Ares Market
Because a Person node with the name “Greta Gerwig” already exists, this query will only SET the dynamic labels added to the ON MATCH subclause. To circumvent possible performance issues, place the dynamic labels or relationship types within ON CREATE or ON MATCH subclauses. For example, MERGE can be used to specify that a graph must contain a node with a Person label and a specific name property.If there isn’t a node with the specific name property, a new node will be created with that name property. At the input layer there are the coded messages (with ngrams), and at the output layer the different types of known and referenced ciphers on dCode.
Merge On A Relationship Between An Existing Node And A Merged Node Derived From A Node Property
Elevate your shopping game and let our aggregator be your guide to the world of exceptional cypher website. At the heart of our vision for the future of cypher url shopping is a deep commitment to empowering cypher mirror connoisseurs. We recognize that the true value of exceptional cypher url lies in the unique stories, craftsmanship, and personalized experiences that they offer. That’s why we’re dedicated to expanding our platform to include a diverse range of specialized cypher onion marketplaces, ensuring that you can discover the most exceptional, one-of-a-kind items that cater to your discerning tastes. Our cypher url aggregator is more than just a platform – it’s a promise of uncompromising quality, customer-centric service, and a shopping experience that redefines the norm.
Node And Relationship Operators
The results of a CASE expression can be used to set properties on a node or relationship. Similar to EXISTS subqueries, path pattern expressions can be used to assert whether a specified path exists at least once in a graph. The XOR operator returns true if exactly one of the two boolean expressions is true, but not both. A COLLECT subquery creates a list with the rows returned by the subquery.COLLECT, COUNT, and EXISTS subqueries can be used inside other clauses.
Caesar Shift Messages
The relationships() function returns a LIST containing all the RELATIONSHIP values in a PATH. The nodes() function returns a LIST containing all the NODE values in a PATH. The graph.byElementId() function is used in the USE clause to resolve a constituent graph to which a given element id belongs.If the constituent database is not a standard database in the DBMS, an error will be thrown. The avg() duration function returns the average of a set of DURATION values. List running transactions (within the instance), returns only the default outputs (database, transactionId, currentQueryId, connectionId, clientAddress, username, currentQuery, startTime, status, and elapsedTime).
- Torrez Market was established in February 2020, making it a fairly novel darknet market.
- Cypher darknet enthusiasts and cypher onion connoisseurs alike will find their perfect match on our platform, and we’re committed to guiding you every step of the way.
- The variety of encoding options keeps things fresh, and it’s really helped spark interest in cryptography among our members.
- Set the default Cypher version for a standard or composite database when creating it.The available versions are CYPHER 25 and CYPHER 5.If not specified, the default language for the database is set to the default language of the DBMS.
- The isEmpty() function returns true if the given LIST or MAP contains no elements, or if the given STRING contains no characters.
Operator traverses one level deeper into the nested structure. The modulo division operation % returns the remainder when one number is divided by another. The subtraction operator – is used to subtract numeric values. List comprehension can be used to remove any unknown NULL values when concatenating LIST values.
The walkthrough for understanding how to identify vulnerabilities like command injection is key. This knowledge aids in decrypting encrypted data and unraveling hidden clues within the Cypher challenges. Understanding the intricacies of this challenge on HackTheBox will elevate your cybersecurity skills. Cypher introduces you to the world of cryptography and graph database vulnerabilities, including various query techniques. Mastering Cypher involves deciphering encrypted messages, exploring directories, and exploiting server weaknesses. By delving into this realm, you’ll enhance your ability to identify and mitigate potential security threats.
Expansive And Distinctive Product Range
Our anonymous aggregator service ensures you get the best deals, with the convenience of a single platform. Experience the ultimate shopping experience and unlock the secrets of the most successful cypher url marketplace. As the premier destination for cypher darknet enthusiasts, we’re constantly innovating and evolving to meet the demands of our discerning customers. Our platform is designed with the future in mind, incorporating the latest advancements in e-commerce technology to provide you with a seamless and efficient shopping experience. From lightning-fast search functionalities to intuitive personalization features, we’re committed to making your cypher link journey as smooth and enjoyable as possible.
Hydra Market Darknet
Clicking Soos’s upper body enough times had a random chance of yielding a Bill-possessed Soos, and an encoded message reading “! ! !” (translates to “SO! MANY! QUESTIONS!”note 11). The text is not encoded in a familiar cipher from the series, but rather in the font 1651 Alchemy Symbols by GLC.2 This font is also used a few times as a cipher in The Book of Bill. Grant SHOW PRIVILEGE privilege to list privileges to the specified role. Grant REMOVE PRIVILEGE privilege, allows the specified role to remove privileges for roles.
List all databases in Neo4j DBMS and information about them, returns only the default outputs (name, type, aliases, access, address, role, writer, requestedStatus, currentStatus, statusMessage, default, home, and constituents). The localtime.realtime() function creates a LOCAL TIME instant. Function returns the current LOCAL TIME instant using the realtime clock.
Create a new user and set the password using the auth provider syntax. Remove all databases from the specified server, adding them to other servers as needed. The specified server is not allowed to host any new databases. Only allow the specified server to host databases in primary mode. The time.truncate() function truncates the given temporal value to a ZONED TIME instant using the specified unit. Map projection with an all-map projection to project all key-value pairs from a MAP without explicitly listing them.